So, your crypto's been stolen. The first question that hits you is a gut-wrenching one: "Can I get it back?" The short answer is yes, it's often possible, but it's nothing like calling your bank to reverse a credit card charge. This is a whole different ballgame.
Unlike traditional finance, crypto transactions are irreversible. But here’s the twist: the blockchain, the very technology that makes it decentralized, also creates a permanent, public trail of evidence. Every move the thief makes is recorded forever. Think of it less like cash vanishing into thin air and more like a stolen car with a screamingly obvious GPS tracker—we can follow the trail.
What Makes a Recovery Successful?

Whether you get your crypto back comes down to a few critical things. It’s not a coin flip; success depends entirely on the specifics of the theft and, most importantly, how fast you move. That permanent record on the blockchain is our starting point for every single recovery attempt.
Key Factors That Tip the Scales
Your chances of getting your funds back really boil down to a handful of variables. Getting a handle on these will help you set realistic expectations right from the start.
- Speed of Action: The clock is your biggest enemy. The first 24-48 hours are absolutely critical. Acting fast gives us the best chance to freeze the funds before they get mixed, tumbled, or laundered through a web of decentralized services.
- Where the Funds Landed: This is huge. If the thief sends the crypto to a major, regulated exchange—one with Know-Your-Customer (KYC) rules—our odds of recovery shoot way up. If they send it to a privacy mixer or a decentralized exchange, the chase gets much harder.
- The Nature of the Attack: How did they get in? A simple phishing scam leaves a different trail than sophisticated malware or a DeFi protocol exploit. Each scenario requires a unique strategy.
To give you a clearer picture, here's a quick breakdown of what helps or hurts a recovery case.
Crypto Recovery Feasibility at a Glance
| Factor | High Recovery Chance | Low Recovery Chance |
|---|---|---|
| Speed | Reported within 24-48 hours | Days or weeks have passed |
| Destination | Sent to a regulated CEX (e.g., Coinbase, Binance) | Sent to a privacy mixer, DEX, or private wallet |
| Amount | Substantial enough to justify legal/forensic costs | Small "dusting" amounts |
| Evidence | Clear transaction IDs, scammer's address, chat logs | Vague details, no transaction hashes |
| Jurisdiction | The thief's exchange is in a cooperative country | The exchange is in an uncooperative jurisdiction |
Ultimately, a strong case has speed and a clear trail on its side, while a weak one has been sitting for too long or has hit a dead end at a privacy service.
The Team You Need on Your Side
Recovering stolen crypto is a team sport, not a solo mission. It takes a coordinated effort from several key players to trace and claw back your assets.
The entire strategy for crypto recovery is about using the blockchain's transparency against the criminals. We meticulously map the flow of stolen funds to find the choke points—usually centralized exchanges—where we can work with them and law enforcement to intercept and freeze the assets.
This isn't something one person can do alone. A real recovery effort involves:
- Blockchain Forensic Specialists: These are the on-chain detectives. Firms like ours use powerful analytical tools to trace the path of stolen funds, even as thieves try to cover their tracks across different blockchains.
- Centralized Exchanges (CEXs): A cooperative exchange is your best friend in a recovery. When we present them with solid evidence, they can freeze accounts and assets tied to the crime, stopping thieves from cashing out.
- Law Enforcement Agencies: You need to file an official report. Involving agencies like the FBI gives us the legal muscle to issue subpoenas and court orders, compelling exchanges to cooperate and seize the funds.
In 2025 alone, the crypto world lost over $3.4 billion to hacks and scams. It's a staggering figure. But the story doesn't end there—recovery efforts are getting smarter and more effective. Global initiatives successfully seized $2.4 billion of that stolen money last year. In fact, industry data from firms like Chainalysis shows that nearly 70% of stolen funds in reported cases are eventually returned, thanks to the combined power of private forensics, exchange cooperation, and law enforcement action.
How Crypto Tracing Unravels the Digital Heist
Think of stolen crypto like cash that’s been secretly dusted with invisible, fluorescent dye. The moment it’s touched or moved, it leaves a permanent mark. Crypto tracing follows this same idea, but the "dye" is the indelible public record of every transaction on the blockchain.
This entire process is called on-chain analysis, and it’s how we follow the digital breadcrumbs. Our investigators use sophisticated analytical tools to map out the journey of stolen funds, piecing together seemingly random wallet addresses to tell the full story. Each transaction is another clue that helps us chart the thief’s path.
The blockchain’s public nature is our single greatest advantage. While wallet addresses are pseudonymous—meaning they aren’t directly tied to a name like a bank account—they are far from anonymous. The whole point of on-chain analysis is to peel back that pseudonymity and link those addresses to real-world people or entities.
Mapping the Flow of Stolen Funds
The first step is always to pinpoint the exact transaction where the theft occurred. From there, forensic specialists begin tracing the crypto as it jumps from one wallet to the next. Thieves almost always try to cover their tracks by moving funds rapidly through dozens, sometimes hundreds, of different wallets in a technique known as "chain hopping."
This frantic movement actually creates a massive amount of data. To a trained analyst, this flurry of activity is a dead giveaway of illicit behavior. Forensic software helps us visualize these movements, creating a clear map showing how the funds flowed from the victim's wallet to where they sit now. You can even get a head start on this yourself with public tools. To see how, check out our guide on what a blockchain explorer is and how to use it.
The most critical moment comes when the thief tries to cash out the stolen crypto for traditional money, like dollars or euros. To do this, they almost always have to send the funds to a centralized exchange (CEX).
These exchanges function as critical "choke points" in the crypto ecosystem. They are the bridges connecting the digital asset world to the traditional financial system, and they represent our best chance to intercept the funds.
The Power of Exchange Cooperation
Once stolen crypto lands on a CEX like Coinbase or Binance, the rules of the game change entirely. These platforms are regulated financial institutions, which means they are legally required to have Know-Your-Customer (KYC) and Anti-Money Laundering (AML) protocols in place. In short, they collect identity documents from their users.
When our forensic investigators confirm that stolen funds have been sent to an account on a CEX, we can present our evidence to the exchange and to law enforcement. From there, the exchange can take decisive action:
- Freeze the Account: The exchange will immediately place a hold on the thief's account, preventing them from withdrawing or trading the assets.
- Identify the User: Using their KYC data, the exchange can often pinpoint the real person or group behind the account.
- Cooperate with Law Enforcement: With a valid subpoena or court order, the exchange provides the user's details and helps authorities seize the assets.
The rise of AI-powered crypto fraud has fueled a massive $14 billion criminal industry. But it’s this very transparency that allows experts to fight back effectively. Success comes down to speed—the faster stolen assets hit a KYC-compliant exchange, the higher the recovery rate, because these platforms must cooperate with legal authorities. Conflict International offers more insights into how blockchain forensics is used to unmask these criminal schemes.
When you realize your crypto is gone, the feeling is a punch to the gut. But panic is your enemy here. What you do in the first 24 to 48 hours is absolutely critical and can make or break any chance of recovery. Acting quickly and methodically gives you the best shot at tracing the funds before they vanish into mixers or other laundering services.
Your first job is to preserve every single piece of digital evidence. You have to think like a crime scene investigator—every detail is a potential clue. Don't delete a thing. This data is the bedrock of any investigation and the first step toward potentially getting your crypto back.
The Emergency Checklist: Preserve and Report
You need to immediately start building a detailed record of the theft. This information is non-negotiable for reporting the crime and bringing in professional help.
- Document Everything: Get your transaction IDs (also called hashes), the thief’s wallet address, your own wallet address, and the precise date and time the theft occurred. Take screenshots of any scam websites, conversations, or phishing emails involved.
- Report to Your Exchange: If a centralized exchange was part of the transaction, contact their support team right away. Give them all the details you've collected. A fast report might lead them to freeze the thief's account if the funds are still sitting there.
- File a Police Report: Call your local police and file an official report. They might not be crypto experts, but getting a police report number is a vital piece of documentation you'll need for later legal or exchange-related actions.
- Report to Federal Agencies: In the United States, you should also file a report with the FBI's Internet Crime Complaint Center (IC3). This agency specializes in cybercrime and uses the data to identify and track larger criminal operations.
This process gives you a high-level view of how stolen funds are traced, from the moment of theft toward a potential asset freeze.
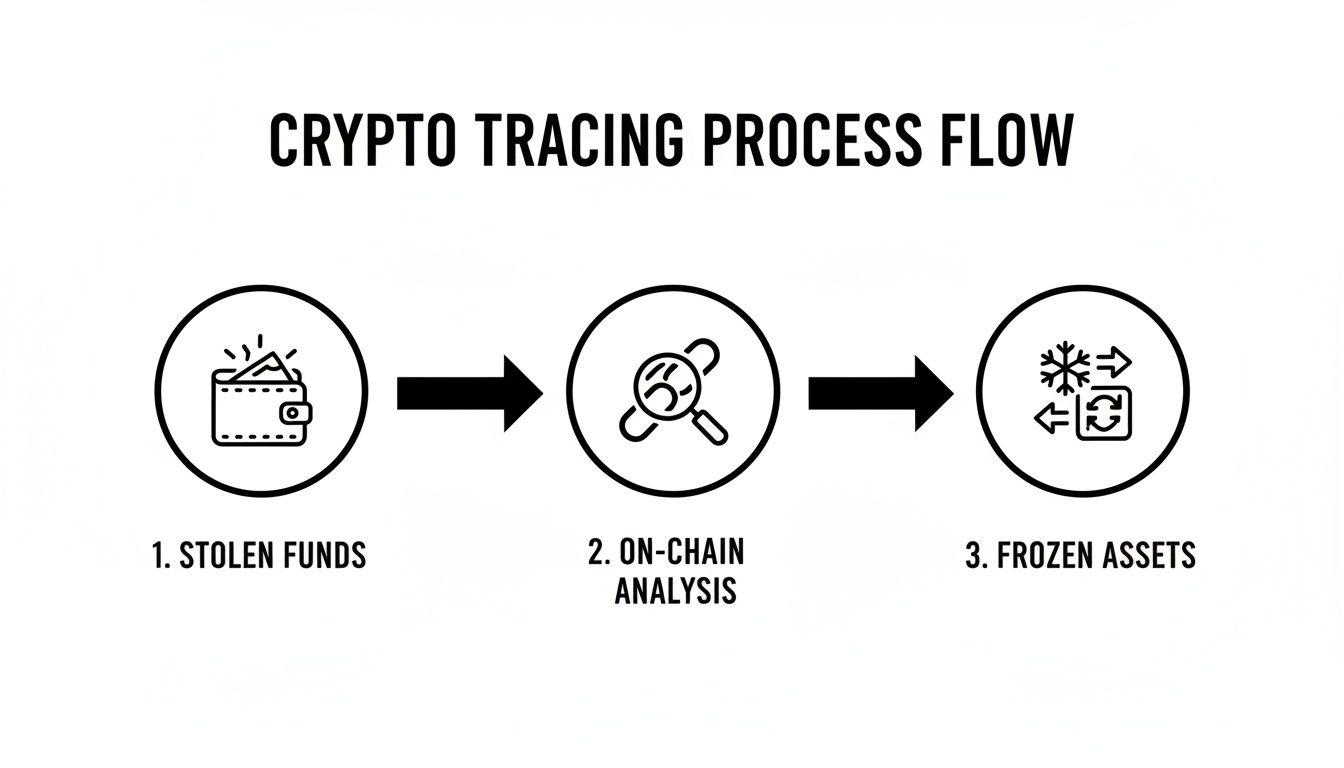
As the graphic shows, the path from theft to recovery depends entirely on successfully analyzing on-chain data to find where the funds went, which is what makes intervention possible.
Engaging Professional Help
Once you've completed those initial steps, it's time to consider hiring a professional crypto recovery or forensic service. Law enforcement and exchanges have a role to play, but their resources are often stretched incredibly thin. A specialized firm can bring dedicated tools and expertise to conduct a thorough investigation.
The simple truth is that time is working against you. The more you wait, the more chances a thief has to obscure the trail using tumblers, mixers, or cross-chain bridges. A professional can start the tracing process almost immediately.
When you look for help, find a service that specializes in on-chain forensics. They will use the evidence you gathered as the starting point to trace your stolen assets across the blockchain. Their goal is to track the funds through intermediary wallets and identify the exact point they land on a centralized exchange—this is the critical "choke point" where assets can be frozen. Making the right moves in this brief window is your strongest play in a crisis.
Building a Rock-Solid Evidence Case File
When you're fighting to get your stolen crypto back, your most powerful weapon is a well-organized case file. Think of it as a pre-packaged investigation—every detail, no matter how small, becomes a vital clue for law enforcement and recovery specialists.
A complete file is what turns a messy situation into a clear, actionable case. It allows investigators to move quickly, connecting the dots and chasing down leads before the trail goes cold.
The goal is simple: transform raw data into a tool for justice. A thoroughly documented case gives you a fighting chance, dramatically shortening the investigation and improving the odds of recovery.
Your Essential Evidence Checklist
To give investigators the ammunition they need, you need to be methodical. Start gathering these critical items immediately:
- Transaction Hashes (TXIDs): This is the single most important piece of evidence. It's the unique ID for the theft on the blockchain and the starting point for any on-chain analysis.
- Thief's Wallet Address(es): The exact destination address where your funds were sent. Copy the full string of characters with perfect accuracy.
- Your Wallet Address: The address from which the funds were stolen.
- Timestamps: Note the exact date and time the transaction occurred. The more precise, the better.
- Communication Records: Screenshot everything. Every email, text, social media DM, or app-based chat with the scammer can help establish fraudulent intent.
Documenting the Digital Crime Scene
Beyond the core data, you need to paint a picture of how the theft happened. This context is crucial; it helps investigators understand the scammer’s methods, which can often link them to larger criminal rings.
Professional investigators use specialized tools to visualize this data. This image shows the interface of TRM Labs, a leading blockchain intelligence platform that visualizes the flow of stolen funds.
This isn't just about making a pretty chart. Tools like this trace the path of your crypto from wallet to wallet, ultimately trying to find where the thief cashes out—usually at an exchange where the assets can be frozen.
This kind of evidence trail produces real results. In one notable case, the Houston Police Department used TRM Labs to trace $150,000 in stolen Ethereum through a complex web of wallets. The trail led them to a single exchange account.
Based on that digital evidence, they successfully froze $300,000 in the thief's account and returned the victim's funds. It was one of Texas's first successful crypto recoveries of its kind, and it all started because the victim acted fast and provided a clear, actionable evidence package. You can explore the details of this successful cryptocurrency tracing and recovery to see how it played out.
Here’s a completely rewritten version of the section, designed to sound like it was written by an experienced human expert.
How to Choose a Recovery Service and Dodge the Scams
In the frantic hours after you realize your crypto is gone, your first instinct is to find help. Fast. But you have to be careful. That feeling of desperation is exactly what a second wave of predators—fake recovery services—are banking on.
These scammers are experts at targeting victims when they're most vulnerable. They promise a quick fix, a guaranteed return of your funds, all while setting you up for another devastating loss. Learning to spot these frauds and find a legitimate expert is the most important next step you can take.
Theft Recovery vs. Access Recovery: Know What You Actually Need
Before you even start looking for help, you need to understand a critical distinction. There are two fundamentally different types of "recovery," and hiring the wrong one will just waste precious time and money.
Theft Recovery (Forensics): This is for when your crypto was stolen by a scammer or hacker. This work is investigative. It involves deep forensic analysis to trace the stolen funds on the blockchain, identify the culprits, and work with law enforcement and exchanges to freeze and hopefully seize the assets.
Wallet Access Recovery: This is for when you still have the wallet but can’t get into it—maybe you’ve forgotten a password or misplaced a seed phrase. This is what we at Wallet Recovery AI specialize in. We use powerful computational methods to help you regain access to your own funds. We don't trace stolen crypto.
If a thief stole your funds, you need a forensic firm. If you just lost your password, a forensic firm can’t help you, but we can. Knowing the difference is your first line of defense.
Red Flags That Scream "Recovery Scam"
Recovery scammers aren’t very original. They tend to use the same script, making bold promises that are, frankly, impossible to keep. If a service you're talking to does any of the following, walk away.
Any service that guarantees the return of your stolen funds is lying to you. There are no guarantees in this line of work. This is the single biggest red flag, period.
Keep an eye out for these other classic warning signs:
- Upfront "Recovery" Fees: This is the most common trick. They'll demand a fee, a tax, or a percentage of the stolen amount before they do anything. A legitimate firm might have a professional retainer for their time, but they will never ask you to pay a fake "withdrawal fee" to unlock your recovered funds. That’s just a classic advance-fee fraud.
- Asking for Your Private Keys or Seed Phrase: Never, ever, ever give this information to anyone. A legitimate forensic investigator will only need public data, like your wallet address and the transaction IDs, to start tracing the funds. Anyone asking for your keys is just trying to empty whatever you have left.
- Promising to "Hack Back": The idea of a vigilante hacker breaking into the scammer’s wallet to get your money back sounds great in a movie, but it's a fantasy. In the real world, it's illegal, usually impossible, and just a story scammers tell to get you to pay them.
- Hiding Their Identity: Scammers love to operate from anonymous social media accounts and generic, cookie-cutter websites. A real company will have a public-facing team, a verifiable business registration, a physical address, and a professional footprint.
What a Legitimate Firm Looks Like
A genuine crypto forensics company operates like any other professional investigative body. They are methodical, transparent, and work within the established legal and technical frameworks. You can learn more about how to properly vet these services in our guide to crypto scam recovery services.
Here’s a quick-glance comparison of what to look for versus what to run from:
| Characteristic | Legitimate Forensic Firm | Recovery Scam |
|---|---|---|
| Process | Transparent; explains their forensic and legal strategy. | Vague; talks about "hacking" or "secret algorithms." |
| Payment | Clear fee structure, often a retainer for services rendered. | Demands upfront fees, "taxes," or a percentage to "release" funds. |
| Identity | Verifiable company, public team, and real case studies. | Anonymous agents, no public records, and fake testimonials. |
| Information Request | Asks for public data like transaction hashes. | Asks for private keys, seed phrases, or remote computer access. |
Choosing the right kind of help is one of the most important decisions you'll make in trying to figure out if your stolen crypto can be recovered. By arming yourself with this knowledge, you can avoid the painful mistake of becoming a victim twice.
Setting Realistic Expectations for Timelines and Success
Before you do anything else, you need to manage your own expectations. When clients ask, "Can my stolen crypto be recovered?" there's never a quick "yes." A successful recovery is a marathon, not a sprint. Getting yourself mentally prepared for a long and complex process is one of the most important things you can do right now.
The timeline is often frustratingly long. In the best-case scenario—where the thief sends your funds directly to a regulated exchange that cooperates with law enforcement—you might see a resolution in a few weeks or months.
Most cases aren't that simple. If the thief was sophisticated enough to use chain-hopping, crypto mixers, or send funds to an exchange in an uncooperative jurisdiction, the recovery process can easily stretch into years. Patience is not just a virtue here; it's a necessity.
Understanding the Wide Range of Success Rates
There is no single, universal success rate for crypto recovery. The chance of a positive outcome depends entirely on the specifics of the theft—how fast you act, the quality of your evidence, and the skill of the thief.
The single biggest factor determining success is where the stolen funds end up. If they land at a centralized exchange with strict KYC (Know Your Customer) policies, your chances skyrocket. If they enter the decentralized finance (DeFi) ecosystem or get laundered through a privacy mixer, the odds get much, much longer.
Think of it in terms of concrete scenarios. For example, a victim of a pig butchering scam who reports the theft within 24 hours and traces the funds to a major exchange may have a recovery likelihood as high as 90%.
On the other hand, funds stolen in a complex DeFi protocol exploit—where the smart contract code itself was the weapon and assets were instantly scattered across multiple blockchains—often have a recovery chance of less than 10%.
Crypto Theft Scenarios and Recovery Likelihood
To give you a clearer picture, it’s helpful to break down recovery potential based on the type of theft. This isn't guesswork; it's based on years of forensic analysis and real-world case data from 2026.
The table below outlines common theft scenarios and what you can realistically expect.
| Theft Scenario | Recovery Likelihood | Key Success Factor |
|---|---|---|
| Phishing Scam to CEX | High (70-90%) | Victim reports the theft immediately to the exchange and law enforcement. |
| Rug Pull (DeFi) | Very Low (<10%) | The anonymous nature of developers and instant liquidity withdrawal. |
| Exchange Hack | Moderate | Depends entirely on the exchange's solvency and recovery efforts (e.g., insurance). |
| Ransomware Attack | Low-Moderate (15-30%) | Tracing payment to an off-ramp before funds are moved or mixed. |
| Investment Scam (Ponzi) | Moderate | Depends on asset seizure from the scam operator by law enforcement. |
These figures are a framework, not a guarantee. Every "win" in crypto recovery is the result of a long, patient process that often involves forensic experts, legal teams, and international cooperation. Approaching this with a clear, data-driven perspective will help you stay grounded and make the right decisions.
Your Top Questions About Stolen Crypto Recovery
When you've been robbed, you have questions. Lots of them. The panic and confusion can be overwhelming, but getting straight answers is the first step toward figuring out your next move. Here are the frank, no-nonsense answers to the most common questions we hear from victims of crypto theft.
How Long Does Crypto Recovery Actually Take?
There's no simple timeline, and anyone who gives you one is not being honest. The process can range from a few weeks to several years.
A best-case scenario? The thief moves your funds directly to a cooperative, regulated exchange, and you report it immediately. In that rare case, resolution might take a few months. But that’s the exception.
Most investigations are far more complex. If the thief uses tools like crypto mixers, hops between different blockchains, or uses DeFi protocols to obscure the trail, the tracing work becomes incredibly difficult. If the trail leads to an uncooperative exchange in a foreign country, you're looking at a process that can easily stretch on for years, involving international law enforcement and court orders.
Can Crypto Sent to the Wrong Address Be Recovered?
This is a painful but important distinction. Sending crypto to a wrong address is a mistake, not a theft. Because of the way blockchains are designed, these transactions are almost always irreversible. There is no "undo" button.
The only sliver of hope is if you can identify the owner of the receiving address and they are honest enough to return the funds. In the pseudonymous world of crypto, this is practically impossible. A theft leaves a criminal trail to follow; a mistaken transaction, unfortunately, usually just leaves a dead end.
What Is the Difference Between a Forensic Firm and a Wallet Recovery Tool?
It’s critical to know who to call for what. These services solve two completely different problems, and confusing them will cost you time and money.
A forensic firm goes after money stolen by someone else. A wallet recovery tool helps you get back into a wallet you own but are locked out of.
Let’s break it down:
- Forensic Firms: Think of them as private investigators for the blockchain. They trace stolen funds, package evidence for police, and work with exchanges to freeze criminal assets. You hire them after a hack or scam.
- Wallet Recovery Tools: This is what we do. We help when you are the only one who has lost access—maybe you forgot a password, can't find a private key, or have a corrupted wallet file. We use powerful computational methods to break into your own wallet.
Should I Report a Small Amount of Stolen Crypto?
Yes, absolutely. Even if the amount seems insignificant, every single report matters.
Your report might not trigger a full-blown investigation on its own, but it contributes to a much larger picture. Law enforcement and blockchain analysts use this data to connect the dots, identify patterns, and uncover large-scale criminal operations. Your "small" theft could be the missing piece of the puzzle that helps take down a major scammer.
If you've lost access to your wallet due to a forgotten password or lost key—not theft—our team at Wallet Recovery AI can help. We specialize in securely restoring access to your own funds without ever asking for your private keys. You can learn more and request assistance at https://walletrecovery.ai.


Leave a Reply