You open the wallet, type the password you are sure is right, and get rejected.
Then you try the old variations. The one with the year. The one with the symbol. The one you used on that laptop you no longer own. Very quickly, calm turns into panic. That reaction is normal. Bitcoin wallet password recovery is one of the few technical problems where one wrong move can waste time, damage evidence, or expose the wallet to scams.
The hardest part is not always the cryptography. It is the chaos. People usually start by guessing wildly, downloading random tools, and touching the only copy of the wallet file they have. That is how recoverable situations become worse.
The Sinking Feeling of a Locked Bitcoin Wallet
A locked Bitcoin wallet does not feel like a forgotten app login. It feels heavier because there is no support desk waiting to reset your access. If you control the wallet, you also carry the burden of recovery.

For many people, the moment hits late. They finally decide to move funds after years of inactivity, or they plug in an old hardware wallet, or they find a wallet.dat on a backup drive and realize the password is gone. Others discover the problem after a device failure, a move, or the death of a family member who handled everything privately.
This is not rare. Estimates indicate that 3 to 4 million BTC, about 20% of all mined Bitcoin, are permanently lost and unrecoverable, with a value range of $260 billion to $350 billion, according to the reporting summarized at Professional Crypto Recovery’s lost bitcoin analysis. That number matters because it tells you two things at once. First, many people have already been where you are. Second, some wallets are recoverable, but many are not, and the difference usually comes down to what evidence remains.
Panic creates bad decisions
The first wave of mistakes is predictable:
- Repeated blind guessing: People burn time on random password attempts with no pattern.
- Editing or moving files carelessly: A wallet backup gets renamed, overwritten, or copied incompletely.
- Trusting the first “recovery expert” online: Scammers know exactly how desperation sounds.
- Entering seed phrases into websites: This turns a recovery problem into a theft problem.
A seasoned recovery workflow starts from the opposite direction. Slow down first. Inventory what exists. Identify the wallet type. Separate true keys from ordinary passwords. Decide whether you are dealing with restoration, password cracking, file repair, or a dead end.
A practical mindset
A locked wallet is not one problem. It is one of several distinct problems that look similar from the outside:
| Situation | What it really means |
|---|---|
| You have the seed phrase | This is usually a restore job, not a cracking job |
| You have a wallet file but forgot the password | This may be a targeted password recovery case |
| You have a hardware wallet and a forgotten passphrase | Recovery depends on what backups exist |
| You have partial Shamir shares | This is a threshold reconstruction problem |
| You have nothing except a memory of owning BTC | The path is much narrower |
The best first move is not “try harder.” It is “classify the problem correctly.”
That shift matters. Bitcoin wallet password recovery works best when it is treated like evidence handling, not like a slot machine.
First Steps to Triage Your Situation Before You Act
Treat your wallet like a crime scene you are investigating. The goal is to build a recovery dossier before you touch software, run scripts, or test guesses.
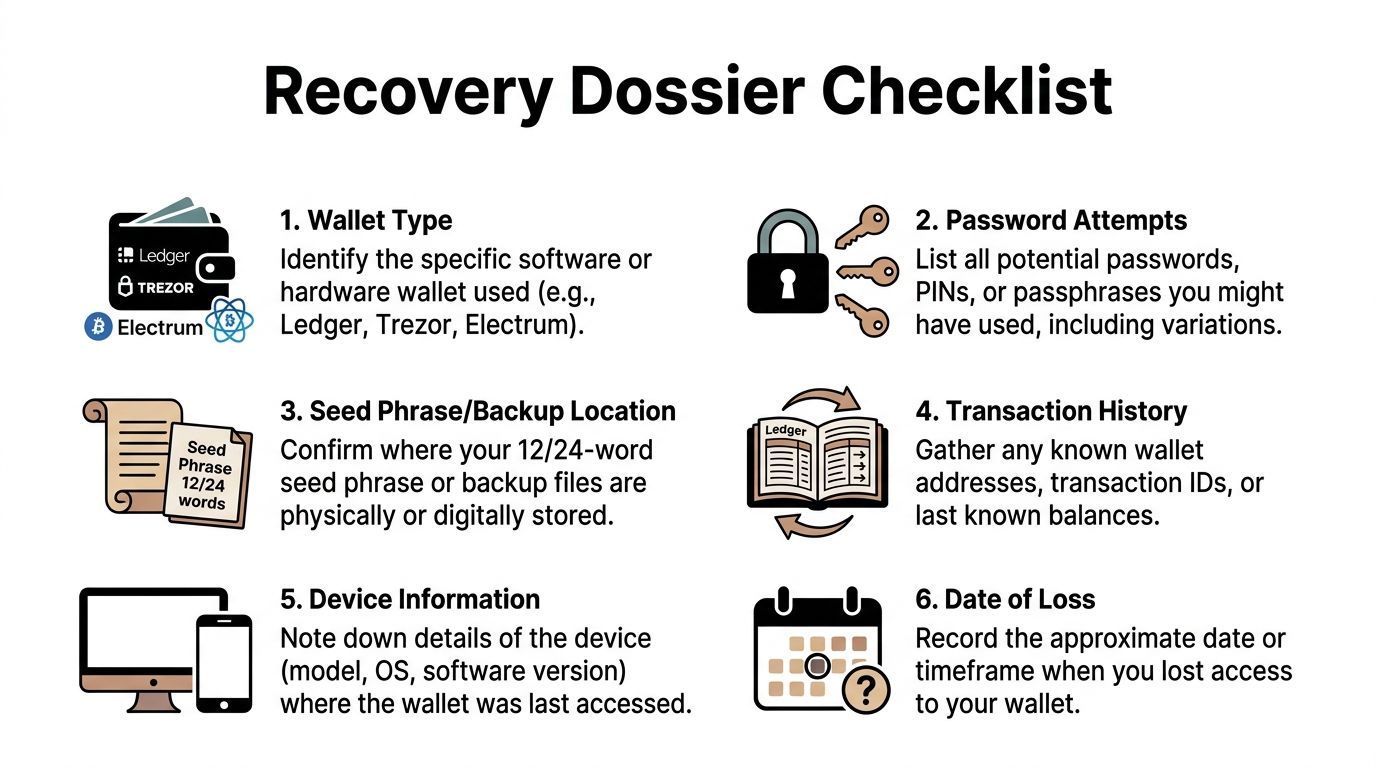
The dossier does two jobs. It preserves details you will forget once stress takes over. It also tells you which recovery path is realistic.
Build the dossier before any recovery attempt
Start with a written record. A text file on a clean machine works. Paper works too.
Capture these details:
Wallet type
Was this Bitcoin Core, Electrum, Blockchain.com, a Ledger or Trezor device, an exchange account, a mobile wallet, or something older that no longer exists? Recovery methods differ sharply by wallet family.What you lost
Did you lose a wallet password, a device PIN, a BIP39 passphrase, a seed phrase, awallet.dat, a keystore JSON, or access to an email tied to a custodial account? People often mix these up. That leads them down the wrong path.What you still have
List every asset you possess: laptop, old phone, hardware wallet, USB stick, paper notes, password manager exports, screenshots, cloud backups, browser downloads, printed PDFs, transaction emails.Approximate creation window
A rough timeframe matters. Old wallets used different formats, defaults, and habits. If the wallet was created during a particular job, move, relationship, or device upgrade, note that too.Known transaction clues
Any receiving address, transaction ID, exchange withdrawal confirmation, or approximate last-known balance helps identify the correct wallet and narrow the timeline.Password fragments
Write down exact fragments, not paraphrases. A leading capital, a favorite suffix, an old handle, a replaced character, a pattern like two words plus numbers. Small details matter.
Use memory reconstruction like an investigator
People dismiss memory work because it sounds soft compared with cracking tools. That is a mistake. For partially remembered passwords, psychological memory techniques can significantly outperform pure brute-force, with some service benchmarks showing higher success rates. A 2026 internal metric cited in the same discussion reported a 50% uplift from AI-prompted cognitive interviews, as summarized by Pocket Option’s discussion of bitcoin recovery methods.
That lines up with what recovery specialists see in practice. Most successful password cases do not start with blind computation. They start with context.
Try reconstructing the moment the password was made:
Where were you living then
City, apartment, hotel, family home. Place names often leak into passwords.What device were you using
Windows laptop, MacBook, Android phone. Device era often predicts your password habits.What was happening in your life
Job title, side project, partner name, travel plans, favorite game, child’s birth year, a phrase you used repeatedly at that time.What did your passwords look like back then
Did you capitalize the first letter? Append years? Use leetspeak? Reuse an email prefix? Add a favorite symbol at the end?What other accounts from that era still exist
Old email logins, forum accounts, exchange accounts, Wi-Fi passwords, archives in browser autofill. If you need a practical starting point for that search, this guide on how to find saved passwords can help surface clues without random guesswork.
Separate safe searching from risky searching
Safe searches are read-only and evidence-based. Risky searches modify files, expose secrets, or create new copies with unknown integrity.
Safe actions include:
- Looking through old download folders
- Checking password managers and browser-saved credentials
- Reviewing old notes, notebooks, and archived cloud documents
- Cataloging devices and backups without opening sensitive files in random software
Riskier actions include:
- Importing a seed phrase into a website
- Running unknown executables from forums
- Opening the only wallet file inside unfamiliar recovery software
- Factory resetting a hardware wallet before confirming backups
If you have only one copy of a wallet file, do not test anything on that original. Make verified copies first and leave the original untouched.
Know what outcome you are aiming for
By the end of triage, you should be able to answer one question clearly: What recovery category am I in?
| Recovery category | Typical next move |
|---|---|
| Seed phrase present | Restore in a compatible wallet, carefully |
| Backup file present, password partial | Build a targeted password strategy |
| Hardware wallet present, no seed | Check whether device access or passphrase clues remain |
| Partial threshold shares | Assess share count and share quality |
| No key material, no real clues | Stop guessing and reassess feasibility |
That discipline saves time. It prevents the two classic failures in bitcoin wallet password recovery: solving the wrong problem, and damaging the only evidence.
Foundational Recovery Paths with Seed Phrases and Backups
If you have a seed phrase or a valid backup file, you are not in an “crack the impossible” scenario. You are in a restore correctly and safely scenario. That distinction matters.
These are the highest-priority paths because they do not depend on guessing a password from scratch. They depend on locating the right recovery material and using it without exposing it.
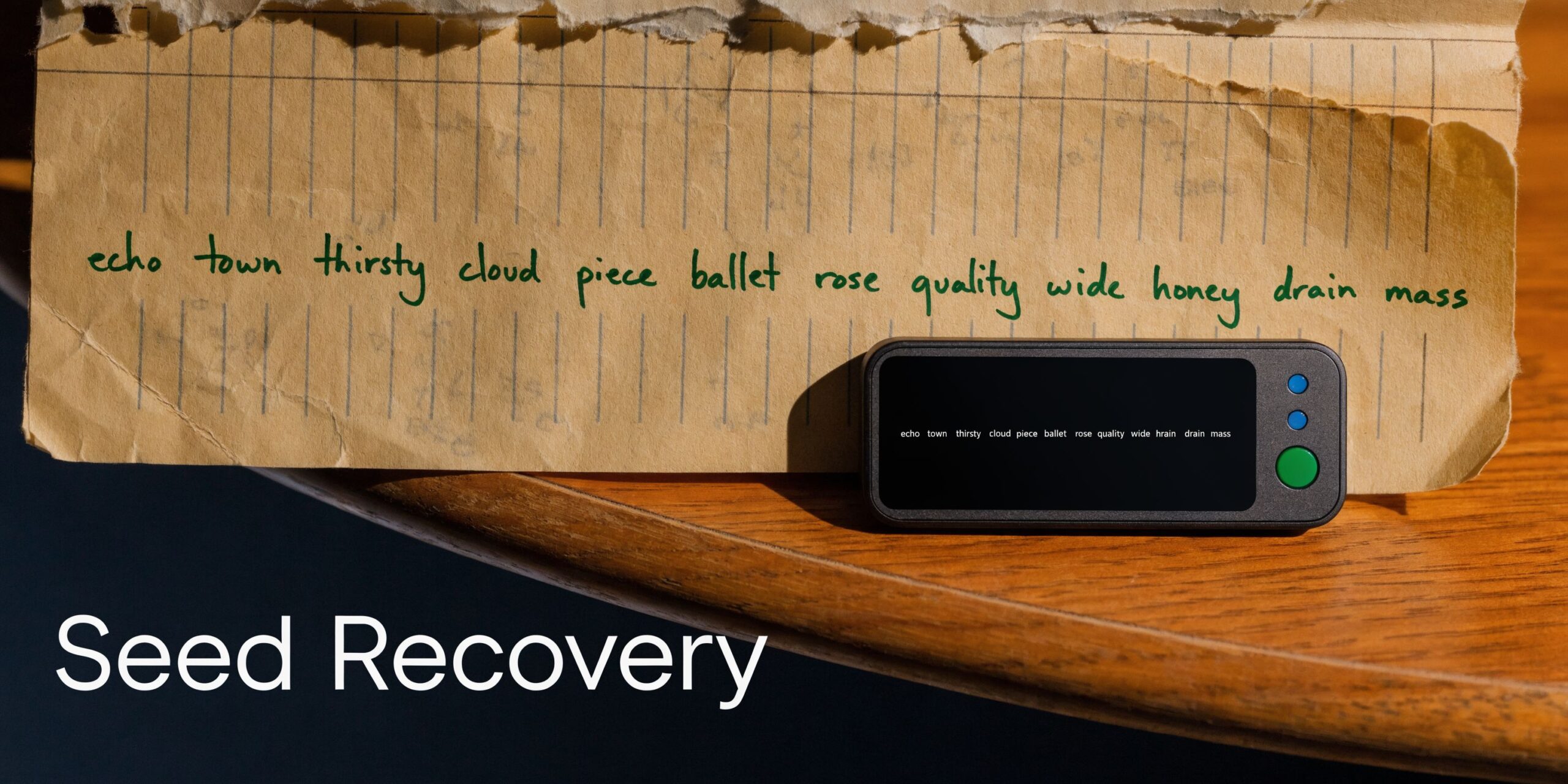
Seed phrase recovery is the cleanest path
A 12-word, 18-word, or 24-word seed phrase is usually the most direct route back into a self-custody wallet. If the phrase is exact and compatible with the wallet’s derivation settings, you are restoring access, not breaking encryption.
Use a careful process:
Choose the correct wallet environment
Restore into the official wallet or a well-understood compatible wallet. Wallets may use different paths and account structures, so “wrong wallet, right seed” can make funds appear missing.Work on a trusted device
Use a clean machine you control. Avoid public Wi-Fi, shared computers, and browser popups. Seed entry should happen in software you trust, not on a website form.Confirm every word and order
Most failed seed restores come from transcription mistakes, wrong word order, or confusion between a seed phrase and an extra passphrase.Watch for hidden passphrases
Some setups use a seed phrase plus an additional passphrase. Without that extra phrase, the wallet restores, but not to the expected balance.Move funds after recovery if exposure is possible
If the seed has ever been stored in email, cloud notes, screenshots, or entered into a questionable tool, assume it may be compromised and migrate funds to a fresh wallet.
A seed phrase is not the same as your wallet app password. The password unlocks the interface. The seed reconstructs the keys.
File-based backups can be just as important
Many older bitcoin wallet password recovery cases center on backup files rather than seed phrases.
Common examples include:
wallet.dat
Typically associated with Bitcoin Core and related workflows.Keystore JSON files
More common in Ethereum ecosystems, but users sometimes misclassify their assets and tools.Exported encrypted backups
Some wallets create proprietary backup files, PDFs, or archives.
With file-based backups, your immediate job is preservation:
- Make multiple copies.
- Keep the original untouched.
- Record where each copy came from.
- Note the device and directory where the file was found.
- Avoid renaming unless necessary for a specific tool, and even then only on a working copy.
If the backup file opens only with a password, you may later move into a targeted recovery process. But the existence of the file itself is a major advantage. It gives you something concrete to test.
Shamir setups need their own triage
Shamir Secret Sharing, often shortened to SSS, solves one problem by creating another. It improves resilience by splitting recovery into threshold shares, but when users lose or damage part of that setup, recovery becomes less intuitive.
This issue is larger than many realize. An often-overlooked challenge in wallet recovery involves SSS. Chainalysis data cited for Q1 2026 says 15% of dormant Bitcoin wallets, representing over $2B in value, use threshold schemes, and 80% of online queries about recovering from partial SSS shares go unanswered, according to the summary at Wallet Recovery Service’s discussion of Shamir recovery gaps.
For a triage-first approach, ask:
- How many shares were originally created
- What threshold was required
For example, a 3-of-5 arrangement behaves very differently from a stricter threshold. - Which shares are physically present
- Are any shares damaged, incomplete, or transcribed manually
- Was an additional passphrase also used
If you do not meet the threshold, there is no simple shortcut. If you do meet it, accuracy matters more than speed. A single bad share or formatting mistake can make a valid setup appear dead.
What works best at this stage
Foundational recovery works when you respect one rule. Do not overcomplicate a restore that should be simple.
If you have the seed phrase, restore. If you have the backup file, preserve it and identify its wallet family. If you have threshold shares, determine whether you meet the threshold before touching tools.
The worst habit at this stage is jumping ahead to brute-force methods because they feel active. In many recoveries, the answer is already in your possession. It is just mislabeled, incomplete, or being used in the wrong environment.
Advanced DIY Recovery Using Specialized Tools
When you do not have a seed phrase, but you do have an encrypted wallet file and meaningful password clues, advanced DIY recovery becomes possible. Many people use the phrase bitcoin wallet password recovery to mean “cracking,” but good recovery work is not random cracking. It is targeted search.

The reason targeted search matters is simple. Pure brute force against strong wallet encryption is often unrealistic. Recovery becomes feasible when you know something about the password structure, file format, wallet age, or generation method.
A real case that shows the pattern
A landmark example involved Joe Grand and Bruno, who recovered a 43.6 BTC wallet, worth about $3 million today, that had been inaccessible for a decade. The password had been generated with RoboForm, and they exploited a flaw in the older generator to recreate the original 20-character password when partial metadata existed, as described in Binance Square’s summary of the Joe Grand recovery case.
The lesson is not that everyone has a hidden software bug waiting to save them. Most do not. The lesson is that recoveries happen when partial information narrows the search space.
The three attack styles that matter
Most serious DIY workflows rely on some combination of these:
Dictionary attacks
A dictionary attack tests lists of likely passwords and variations. Good dictionaries are not giant generic files alone. They are built from your dossier.
A useful list can include:
- old usernames
- favorite phrases
- company names
- pet names
- years that mattered at the time
- common substitutions such as
ato@oroto0. Recovery often succeeds in these situations. People are more consistent than they think.
Mask attacks
A mask attack is useful when the password shape is known but the exact characters are not.
Examples:
- first letter capitalized, then a word, then four digits
- two lowercase words followed by a symbol
- eight characters where the last two are numbers
You are not trying everything. You are trying everything that fits the pattern.
Combinatorial or token-based attacks
This approach breaks the password into chunks and recombines them systematically. It is one of the most practical methods when you know fragments but not order, spelling variation, or appended characters.
This is why tools built around tokens are valuable. They let you test “it probably included this word, maybe this year, maybe one typo” instead of firing blindly at the full universe of strings.
What BTCRecover and Hashcat do
Open-source tools such as BTCRecover, Hashcat, and helper workflows involving bitcoin2john matter because they formalize search rather than improvising it. If you want a non-hype explanation of how these categories fit together, this overview of crypto recovery software is a useful framing resource.
At a high level, the workflow looks like this:
| Tool or component | What it does |
|---|---|
| BTCRecover | Tests structured password candidates against wallet data |
| bitcoin2john | Extracts a crackable hash representation from supported wallet data |
| Hashcat | Runs high-speed password attacks against extracted hashes |
| Your dossier | Supplies the patterns, words, dates, and habits that make the attack realistic |
The practical order usually goes like this:
Preserve the wallet file
Work from copies only.Identify the wallet format
Wrong assumptions break workflows early.Extract or prepare the target
In some cases that means deriving a hash representation from the wallet data.Build a candidate strategy
This is the heart of the job. Generic wordlists alone waste time.Run controlled tests
Start narrow. Confirm the workflow is valid before widening the search.Log results carefully
A professional workflow tracks what was tried, what assumptions changed, and why.
Why most DIY attempts fail
The tools are not the main obstacle. Strategy is.
People fail because they:
- start with giant untargeted lists
- skip wallet identification
- misremember what type of secret they lost
- test on originals
- confuse app passwords with seed phrases or passphrases
- use malware-ridden downloads from random videos and forums
There is also a harder truth. Some passwords are too strong to recover without much better clues. If the password is long, unique, and not built from life-pattern data, computation alone may not save you.
The moment a password search becomes “everything I can think of” instead of “a structured model of what I probably did,” the odds collapse.
Good DIY candidates versus bad DIY candidates
A rough decision frame helps.
Good DIY candidate
- You have the wallet file.
- You know the wallet family.
- You remember part of the password, structure, era, or habits.
- You can work on verified copies.
- You are comfortable following technical instructions exactly.
Bad DIY candidate
- You have no wallet file and no seed.
- You do not know what wallet you used.
- You are unsure whether the funds were on an exchange or self-custody.
- You only remember “it was probably something secure.”
- You are making changes to the only surviving evidence.
A realistic expectation
Advanced DIY recovery is not magic. It is disciplined reduction of uncertainty. The Joe Grand case is famous because it had enough metadata to turn a dead-looking wallet into a solvable one. Most successful recoveries look less dramatic, but they follow the same principle.
Good clues beat raw horsepower. Exact wallet identification beats enthusiasm. Clean evidence handling beats frantic trial and error.
If you have those pieces, specialized tools can be useful. If you do not, adding more compute often just accelerates failure.
Avoiding Scams and Knowing When to Call a Professional
The recovery industry attracts two kinds of people. Skilled specialists, and opportunists who know panic lowers judgment. You need to sort them fast.
The first line of defense is understanding how DIY goes wrong. Analysis of recovery attempts shows that up to 70% of failures can come from users corrupting their only wallet.dat during failed trials, and 30% of failures in some older Blockchain.com-style cases happen because people miss a required second password, according to the breakdown discussed at ReWallet’s article on forgotten Bitcoin Core passwords.
Those are technical failures. Scam failures are worse because they end with theft.
The red flags are usually obvious
A recovery service or tool becomes suspicious when it does any of the following:
Asks for your seed phrase upfront
A legitimate workflow should minimize exposure. If someone wants the seed immediately, they may just want the funds.Promises guaranteed recovery
No honest specialist can promise that.Claims instant success without reviewing the wallet type
Recovery depends on evidence, not slogans.Pushes you to install remote access software immediately
That is often a prelude to compromise.Demands full payment before any technical assessment
Serious cases require evaluation first.Cannot explain the difference between a wallet password, seed phrase, and passphrase
If they confuse the basics, leave.
The line between safe DIY and professional help
You do not need professional help for every case. If you have a confirmed seed phrase and know how to restore it safely, that is usually straightforward. If you have a standard wallet file, partial password knowledge, and strong technical discipline, a careful DIY attempt can make sense.
You should stop and escalate when the risk profile changes.
Call for help when evidence is fragile
This includes:
- your only backup file looks damaged
- the wallet lives on a failing drive
- you found deleted fragments on an old disk
- a hardware wallet behaves inconsistently
- you suspect there are multiple secrets involved and you are not sure which one is blocking access
Call for help when the model is unclear
If you cannot answer basic triage questions, do not improvise. Common examples:
- you do not know whether the funds were on an exchange or self-custody
- you have a recovery PDF from a discontinued wallet ecosystem
- you have partial Shamir material but do not understand the threshold setup
- the wallet may involve an older or unusual format
Call for help when the value justifies caution
High-value recoveries change the math. Even technically capable users often hand off cases when a mistake could destroy the only viable path. That is not weakness. It is risk management.
Professional help is not about giving up. It is about protecting evidence once the case becomes more expensive than your confidence.
What a competent specialist should do
A competent recovery specialist should be able to:
| What to expect | Why it matters |
|---|---|
| Ask precise questions about wallet type and available artifacts | They are diagnosing, not selling blind hope |
| Emphasize copies and evidence preservation | This reduces self-inflicted loss |
| Explain the probable recovery path in plain language | You should understand the method category |
| Acknowledge uncertainty | Honest work includes possible failure |
| Limit unnecessary exposure to secrets | Good process protects you even during assessment |
One practical option in that category is Wallet Recovery AI, which offers AI-assisted recovery support for cases involving forgotten passwords, corrupted files, inaccessible keystores, and multiple wallet types. That does not mean every case is solvable. It means there is a structured path for cases that have moved beyond safe DIY.
What not to do while waiting for help
If you decide to contact a specialist, stop creating new noise:
- Do not keep downloading random tools.
- Do not keep moving the wallet file between devices.
- Do not “test one last thing” on the original.
- Do not share screenshots that expose seed phrases, partial keys, or identifying data unnecessarily.
The cleaner your evidence remains, the better your options stay.
Your Path to Regaining Access and Staying Secure
Most bitcoin wallet password recovery attempts fail for one reason. People start in the middle. They jump straight to guessing, tooling, or outsourcing before they identify what kind of lock they are facing.
The better path is a funnel. Start with what you have. Classify the problem. Preserve evidence. Use the simplest valid recovery route first. Escalate only when the facts justify it.
Bitcoin recovery methods at a glance
| Method | What You Need | Best For | Success Potential |
|---|---|---|---|
| Seed phrase restore | Exact recovery phrase, compatible wallet | Wallets where the key material is already in hand | High when the phrase is accurate |
| Backup file restore | Valid wallet backup and required credentials | Older software wallets and exported backups | Strong if the format is known and the backup is intact |
| Memory-led password reconstruction | Partial password memory and timeline clues | Cases where the password is partly remembered | Good when patterns and habits are recoverable |
| Specialized tool workflow | Wallet file, correct format, targeted password strategy | Technical users with structured clues | Viable when search space can be narrowed |
| Professional recovery | Fragile evidence, corrupted files, unclear wallet type, high stakes | Complex or high-risk cases | Best when the case exceeds safe DIY limits |
What to do right after recovery
If you regain access, do not stop there. Recovery is only half the job. The moment access returns, think like a custodian.
Move methodically:
Create a fresh wallet if exposure is possible
If your seed, password, or backup touched unsafe environments, migrate funds.Document the new setup clearly
Label backups properly. Record wallet type and device details.Store recovery material offline in more than one secure place
Separation matters. One fire, one theft, or one disk failure should not erase everything.Test your backup plan
A backup is only real if you can use it.
What “realistic hope” looks like
Hope in this field is not wishful thinking. It is evidence-based. Partial information can be enough. A backup file can be enough. A remembered pattern can be enough. But only if you stop treating the problem like a panic event and start treating it like a technical investigation.
Some wallets are gone for good. That is true. Some are recoverable with patient, structured work. That is also true.
The difference usually comes down to four questions:
- What exactly is missing?
- What exactly still exists?
- Can you preserve it safely?
- Are you honest about where your DIY ability ends?
That last question matters more than people admit. The smartest recovery decision is often not “do more.” It is “do the next safe thing.”
If you are stuck between partial clues and risky trial-and-error, Wallet Recovery AI is a practical next step. The service handles cases involving forgotten wallet passwords, corrupted files, inaccessible keystores, and other access barriers across major wallet types, using a privacy-conscious assessment process to determine whether a recovery path is realistic before you make the situation worse.


Leave a Reply