That gut-wrenching moment you realize you’ve been scammed is something no one should ever experience. It’s a paralyzing mix of shock, anger, and panic. But what you do in the next few hours can make all the difference between a total loss and a potential recovery. It's time to switch gears from victim to first responder for your own assets.
Your First 24 Hours After a Crypto Scam
Resist the urge to panic. That’s what the scammers want. Your goal right now isn’t to chase them down or figure out how this happened—it’s to staunch the bleeding and preserve every shred of evidence. The first 24 hours are a sprint, and every action you take lays the groundwork for law enforcement, legal help, or professional recovery services.
And don't beat yourself up. Crypto crime is a massive, sophisticated industry. In just one recent year, total thefts hit $3.4 billion, with hackers alone swiping at least $2.02 billion—a staggering 51% jump from the year before. These scams impacted over 80,000 unique victims worldwide, a clear sign that scammers are hitting more people for smaller amounts. For a deeper dive into these numbers, check out the latest crypto crime trends on Chainalysis.
First, Secure What's Left
Your absolute first priority is damage control. If you suspect one wallet is compromised, you have to assume everything connected to it is tainted. That means moving any remaining funds immediately.
- Set Up a Clean Wallet: Create a brand-new wallet on a completely different, secure device. This is the perfect time to get a hardware wallet like a Ledger or Trezor, which is the gold standard for security.
- Move Your Assets, Fast: Transfer any crypto you can salvage from the compromised wallet to your new, clean one. Be ready for gas fees, and don't hesitate—scammers often have bots set up to drain any new funds that land in a wallet they control.
This is a complete security reset. Don’t even think about reusing old passwords or seed phrases.
Critical Takeaway: Creating a new, uncompromised wallet is a non-negotiable first step. It establishes a secure "safe house" for any assets you can salvage, preventing further losses while you build your recovery case.
Next, Go Silent: Cut Off the Scammer
It's so tempting to message the scammer, to yell, to plead, to try and outsmart them. Don’t. Every word you send is another chance for them to manipulate you or squeeze more information out of you.
Block them on every platform—Telegram, WhatsApp, email, social media, everywhere. Cease all contact. This isn't just for your financial safety; it's for your own peace of mind.
Finally, Become a Detective: Document Everything
Your memory will get fuzzy, but screenshots last forever. Start gathering your evidence now while the trail is still warm. This documentation is the single most important thing you'll hand over to the authorities or a recovery service.
Create a secure folder and start collecting:
- Transaction Hashes (TxIDs): Go to a blockchain explorer and copy the ID for every single transaction related to the scam.
- Scammer's Wallet Addresses: Make a list of every address you sent funds to.
- All Communications: Take full-page screenshots of your conversations. Don't crop anything. Make sure usernames and timestamps are clearly visible.
- Websites and Profiles: Save the URLs of any scammy websites, fake social media profiles, or dodgy platforms involved.
You're building a case file. Treat it that way. The more detailed you are now, the better your chances are down the road.
To help you stay focused during this critical window, we've put together a checklist. Follow these steps methodically in the first 24 hours to give yourself the best possible shot at containment and recovery.
Immediate Action Checklist for Scam Victims
| Action Item | Why It's Critical | Pro Tip |
|---|---|---|
| Secure Remaining Funds | Prevents further losses. A compromised wallet is a live threat until emptied. | Create a brand-new wallet on a clean device—preferably a hardware wallet—and transfer assets immediately. |
| Cut All Communication | Stops the scammer from manipulating you further or extracting more information/funds. | Block the scammer on all platforms. Do not engage, threaten, or plead. Just go silent. |
| Document All Transactions | Provides an unalterable record of where your crypto went, which is essential for tracing. | Use a block explorer like Etherscan or BscScan to find and save all transaction hashes (TxIDs). |
| Screenshot All Conversations | Preserves crucial evidence of the scammer's identity, methods, and promises. | Take full-page, uncropped screenshots. Include timestamps, usernames, and profile pictures. |
| List Scammer's Addresses | These addresses are the starting point for any blockchain tracing or investigation. | Copy and paste every crypto address the scammer provided or you sent funds to into a secure document. |
| Secure Your Accounts | The scammer may have access to more than just your wallet (e.g., email, exchange accounts). | Change passwords on all related financial and email accounts. Enable 2-Factor Authentication (2FA) everywhere. |
Once you've worked through this checklist, you've successfully shifted from a state of panic to one of proactive defense. You've secured your remaining assets and built the foundation for the next steps in your recovery journey.
Building Your Case by Collecting Digital Evidence
Alright, the immediate damage is contained. Now it's time to switch gears from first responder to digital detective. A successful recovery isn't built on hope—it’s built on a foundation of cold, hard proof.
Your new mission is to assemble an undeniable dossier of evidence. This needs to be clear, chronological, and compelling enough for law enforcement, lawyers, or professional recovery services to act on. This isn't just about grabbing a few screenshots; it's about methodically piecing together the entire story of the scam, from the first "hello" to the final fraudulent transaction.
Think of each piece of data as a breadcrumb leading away from the crime scene. Let's start gathering them.
Documenting the Digital Trail
First up, you need to capture every scrap of on-chain data related to the theft. These are the immutable facts of your case, the things nobody can argue with. Your primary tools for this are blockchain explorers like Etherscan (for Ethereum) or BscScan (for BNB Chain).
Here's exactly what you need to hunt down and save:
- Transaction Hashes (TxIDs): Every time crypto moves, it gets a unique ID. Copy and save every single TxID for the transactions you sent to the scammer.
- Scammer Wallet Addresses: Make a meticulous list of every single wallet address you sent funds to. Check it, then check it again. One wrong character and the address is useless.
- Your Wallet Addresses: Don't forget to document the addresses you sent the funds from. This completes the picture for anyone investigating the flow of crypto.
This on-chain data is the skeleton of your case. It’s the concrete, verifiable proof of where your funds went and when.
Preserving Communication Evidence
While the blockchain data tells us what happened, your communication history tells the how and who. Scammers are experts at covering their tracks—they delete messages, block accounts, and vanish into thin air once the job is done. You have to move faster.
Take high-quality, full-page screenshots of every interaction you had with them, across every single platform.
This means getting everything:
- Messaging Apps: Capture the entire conversation from Telegram, WhatsApp, or Signal. Make sure their username, profile picture, and the full chat history with timestamps are crystal clear.
- Social Media: Screenshot any direct messages on Instagram, X (formerly Twitter), or Facebook. Just as important, grab the URL of the scammer's profile before it inevitably disappears.
- Emails and Websites: Save complete emails, including all the header information. If a phony website was part of the scam, save the URL and take screenshots of its main pages.
Pro Tip: Don't just snap a picture of one part of a chat. Use your browser's "full-page screenshot" feature or an extension to capture the whole conversation in one continuous image. This preserves the context and flow, which is absolutely crucial for investigators.
Organizing Your Evidence into a Timeline
You've got a pile of raw data. Now what? A jumbled folder of files won't get you very far. The next step is to get organized and create a structured timeline. A simple document or spreadsheet that lays out the events chronologically is perfect.
Here’s a quick example of how to structure it:
| Date & Time | Event | Evidence Link/File |
|---|---|---|
| Nov 10, 2:15 PM | Initial contact from "CryptoGuru" on Telegram. | telegram_chat_01.png |
| Nov 11, 9:30 AM | Sent 0.5 ETH to their "investment" address. | TxID: 0xabc... |
| Nov 12, 11:00 AM | Received fake "profit" statement via email. | email_statement.pdf |
| Nov 14, 4:00 PM | Sent final 1.0 ETH; scammer blocked me. | TxID: 0xdef... |
This organized dossier turns a bunch of scattered data points into a coherent story. It's the single most powerful tool you have for a credible crypto scam recovery attempt, making it easy for anyone to understand exactly what happened, step-by-step.
How Blockchain Tracing Actually Works
Trying to follow stolen crypto on the blockchain can feel like you're staring at an impossible puzzle, but the basic idea is a lot simpler than you might think. The blockchain is, at its core, a public and permanent ledger. Every single transaction, whether it's buying a coffee or a multi-million dollar hack, is recorded for anyone to see. In a scam situation, this transparency is your single greatest advantage.
Think of it as a digital breadcrumb trail. Scammers do their best to cover their tracks, but they can never truly erase them. On-chain analysis is just the process of following those breadcrumbs from your wallet to theirs, and then seeing where the money goes from there. It’s all about piecing together the story of the theft, one transaction at a time.
This flowchart breaks down the essential evidence you need to get started.
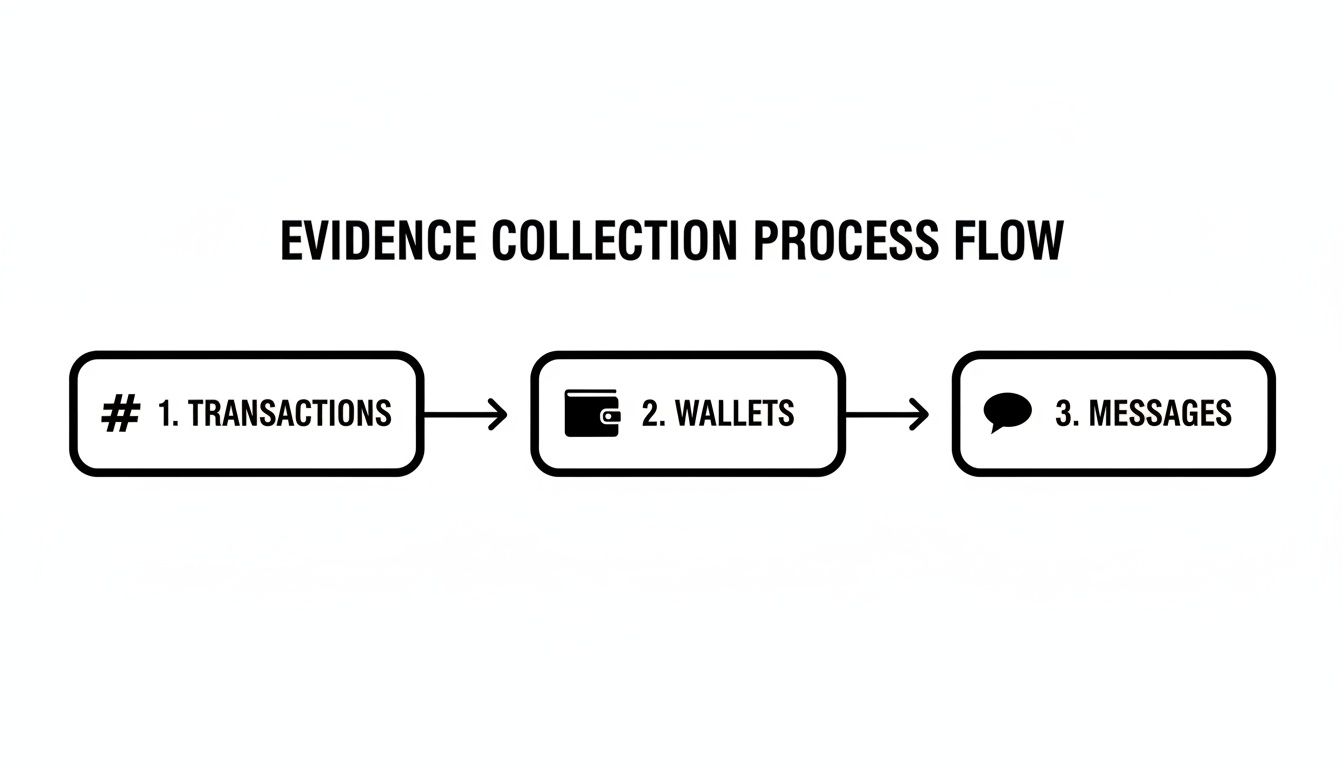
As you can see, the transaction hashes, wallet addresses, and your communication logs are the three pillars of any solid recovery investigation.
Your Essential Tool: Blockchain Explorers
To start this journey, you need a map. In our world, that map is a blockchain explorer. These are powerful (and free) websites that let you search and view any transaction on a given blockchain.
The most famous one for Ethereum and related tokens is Etherscan. For other big players, you’ll want to check out:
- Blockchain.com Explorer: The go-to for Bitcoin.
- BscScan: For anything on the BNB Smart Chain.
- Solscan: For tracking activity on the Solana network.
You just copy and paste a transaction hash (TxID) or a wallet address into the search bar. The explorer will pull up a detailed record showing who sent what to whom, how much, and the exact time it happened. It’s all there.
The key details to zero in on are the "From" and "To" addresses. These show you the direct flow of your funds and give you the next link in the chain to investigate.
The Cat-and-Mouse Game: Mixers and Tumblers
Scammers know they're being watched, so they use special tools to launder the stolen crypto and try to break that breadcrumb trail. The most common are mixers or tumblers. These services work by pooling crypto from tons of different users, jumbling it all up, and then spitting it out to new, clean addresses. The goal is to make it impossible to connect the dirty money coming in with the clean money going out.
But even mixers aren't a silver bullet for criminals. Professional tracers use advanced analytics software to spot patterns and de-anonymize transactions coming out of these services. It’s a constant battle of wits, but the permanent, unchangeable nature of the blockchain means investigators always have a record to work with.
While the tactics are always evolving, the sheer scale of this problem is staggering. We've seen scammers shift from small, frequent rug pulls to much larger, more devastating attacks. In just a single year, losses from rug pulls shot up to nearly $6 billion from only $90 million. This is part of a much bigger trend, with the FBI now reporting over $16 billion in annual cybercrime losses. If you want to dive deeper, you can explore the full analysis on crypto scam trends.
What Professional Tracers See That You Don't
While you can definitely follow the first few hops yourself using an explorer, professional recovery services take this analysis to a whole other level. They use sophisticated software to create visual maps of how the funds are moving, which helps them identify critical patterns you'd almost certainly miss with a manual search.
Key Insight: Professional tracers don't just follow a single transaction. They map out entire networks, looking for connections to wallets already known to be part of scams, high-risk exchanges, or darknet markets. Their main objective is to find the "cash-out" point—where the scammer tries to move the funds onto a regulated, centralized exchange.
These exchanges are required by law to have Know Your Customer (KYC) procedures. This means if stolen funds land in an account on one of these platforms, law enforcement can issue a subpoena to get the real-world identity of the account holder. This is the ultimate goal of most blockchain tracing efforts: linking a anonymous on-chain address to a real person.
Reporting the Crime to the Right Authorities
It’s easy to feel paralyzed after a scam, but taking official action is one of the most important things you can do. I get it—the decentralized world of crypto adds a whole new layer of complexity, but law enforcement agencies are catching up fast. Think of your report as a critical puzzle piece they can use to map out and take down larger criminal rings.
A lot of people I talk to hesitate, figuring their report will just disappear into a black hole. That’s a common misconception. Every single report helps authorities connect the dots, identify patterns, and build much stronger cases against organized fraud operations. Your evidence might be the very thing that links a dozen other victims to the same scammer.
Where to File Your Official Reports
You'll want to start with the national and international agencies that live and breathe cybercrime. These are the big guns, the ones with the jurisdiction to chase criminals across state lines and international borders—which is exactly where most crypto scams operate.
- The FBI's Internet Crime Complaint Center (IC3): This is your first stop in the United States. When you file a report with the IC3, your case enters a federal database that law enforcement all over the country can tap into. Be meticulous when you fill out their online form.
- The Federal Trade Commission (FTC): The FTC is all about tracking fraud and consumer complaints. Reporting here helps them spot emerging trends and blast out public warnings, which could stop someone else from getting hit by the same scam.
- International Agencies: If the scam has roots overseas, look into reporting to agencies in those countries. Good examples include the UK's Action Fraud or the equivalent cybercrime unit in the relevant nation.
Before you start filing, have your evidence dossier ready to go. You’ll need to hand over all the transaction hashes, scammer wallet addresses, and communication logs you’ve gathered. The more precise and organized your information is, the more likely it is that they can take action.
Don't Forget Your Local Police
It's also a good idea to file a report with your local police department. They might not be blockchain experts, but having a local police report number can be surprisingly important for legal or banking reasons. It officially documents the theft, which can be crucial for insurance claims, tax deductions, or proving your case to financial institutions.
The sheer scale of crypto crime is staggering. In just the first quarter of a recent year, losses skyrocketed to $1.77 billion. The main culprits were phishing attacks, responsible for 45% of incidents, and investment scams, which made up another 30%.
When to Bring in a Legal Professional
If you’re dealing with a substantial loss, it's time to talk to a lawyer specializing in digital asset recovery. These aren't your average attorneys; they understand the unique mess of crypto crime and know how to navigate the system effectively.
A Pro Tip From Experience: A good lawyer can open up avenues for civil recovery, like filing a lawsuit to freeze or seize assets if they can be traced back to a person or company. They can also be your bulldog, interfacing directly with law enforcement and exchanges to make sure your case doesn't get lost in the shuffle.
Look, engaging with the authorities is a marathon, not a sprint. By methodically filing these reports, you’re not just fighting for your own funds—you’re contributing to the broader battle against crypto crime. For a deeper dive into what to do after a theft, check out our complete guide on how to recover stolen crypto.
Look, while tracing funds yourself and filing reports are essential first moves, some situations are just too complex to handle alone. We're talking about cases where funds are bounced across multiple blockchains, laundered through sophisticated mixing services, or the losses are life-altering.
When you're in that deep, it's time to consider calling in a professional. But here's the harsh reality: this space is filled with sharks who see your desperation as an opportunity to scam you again.
Making the choice to hire help is a big one. You're handing over sensitive details and putting your trust in a team to hopefully get your assets back. The only way to do this safely is with extreme caution and a solid vetting process. A legitimate firm is a partner, not a miracle worker. They use advanced tools and existing relationships with law enforcement to untangle messes most of us couldn't even begin to understand.
When to Seriously Consider Professional Help
Not every stolen crypto case needs a full-blown recovery team. But if you find yourself in any of these scenarios, it’s probably time to make the call.
- Significant Financial Loss: When the numbers are high, investing in a professional service with a much better chance of success just makes sense.
- Complex Transaction Trails: Did the scammers use a mixer like Tornado Cash? Did they bridge your funds from Ethereum to Bitcoin? If so, trying to trace that manually is a dead end.
- International Scams: If the scam involves people or exchanges in different countries, you need a team that knows how to navigate the jurisdictional nightmare of working with various international law enforcement agencies.
- Wallet Access Issues: Sometimes it's not theft, but a technical lockout. Experts can help with things like recovering a forgotten hardware wallet password or piecing together a corrupted seed phrase.
Spotting the Scammers A Mile Away
The absolute biggest danger you face after getting scammed is the "recovery room" scam. These are fraudulent outfits that pop up, preying on your hope and promising the world. They'll charge you for "services" they have no intention of providing.
Once you know their playbook, their tactics are painfully obvious.
Critical Warning: Be incredibly suspicious of anyone contacting you out of the blue. If someone slides into your DMs on X or Telegram claiming they saw your post and can get your money back, it's a scam. 100% of the time. Real firms will never, ever solicit business this way.
Your best defense is to vet every single potential service mercilessly. If you see even one of these red flags, run.
- Upfront Fees: This is the #1 tell. Legitimate firms almost always work on a contingency fee basis. That means they take a percentage of what they successfully recover. If they're demanding a hefty payment in crypto before they've done a single thing, they're just setting you up for another hit.
- Guarantees of Success: Nobody can guarantee a 100% recovery. The crypto world is too wild and the legal process is too slow. Anyone making absolute promises is lying to get your money.
- Requests for Private Keys or Seed Phrases: Never. Ever. Share. Your. Keys. A real recovery service does not need your private keys or seed phrase to trace stolen funds on a public blockchain. Asking for them is like a locksmith asking for the master key to your entire life.
- Vague Methodologies: If they can't give you a straight answer about their process—how they trace, how they coordinate with law enforcement, what tools they use—it’s because they don’t have one.
The difference between a real firm and a scam is night and day. Before you even start looking, it's a good idea to understand what a professional cryptocurrency recovery firm actually does so you have a solid baseline for comparison.
To make it even clearer, I've put together a table to help you spot the difference between a real specialist and a predatory scammer.
Vetting a Crypto Recovery Service
| Attribute | Legitimate Service (e.g., Wallet Recovery AI) | Scam Operation (Red Flag) |
|---|---|---|
| Payment Model | Works on a contingency basis (a percentage of recovered funds). No recovery, no fee. | Demands a large, non-refundable upfront fee, usually in crypto. |
| Promises Made | Offers a realistic, honest assessment of your case and its probability of success. | Guarantees a 100% successful recovery, no matter the circumstances. |
| Transparency | Clearly explains their tracing methodology, legal process, and how they cooperate with authorities. | Uses vague, technical-sounding jargon to sound impressive without saying anything concrete. |
| Credentials | Has a professional website, public case studies, media mentions, and a verifiable business registration. | Operates from anonymous social media accounts or a cheap, generic-looking website. |
| Data Security | Will never ask for your private keys or seed phrase for blockchain analysis. | Insists they need your seed phrase or private keys to "access" or "unlock" the stolen funds. |
Memorize these differences. Trusting the wrong people at this stage can be more devastating than the initial theft itself. Choose wisely.
Building Your Defenses to Prevent Future Scams

The best way to handle crypto scam recovery is to make sure you never need it. Going through a scam is a painful lesson, but it’s one you can use to build a powerful defense strategy. This isn't about being paranoid; it's about developing a resilient security mindset to protect your assets from the next wave of threats.
Let's take a hard look at your security habits and plug any gaps. Your first line of defense, and often the weakest link, is your wallet. Not all wallets are created equal, and if you're serious about crypto, understanding the difference is non-negotiable.
Fortify Your Wallet Security
A "hot wallet" is always connected to the internet. It's convenient for everyday transactions, but that constant connection leaves your private keys vulnerable to online attacks. A "cold wallet," on the other hand, keeps your keys completely offline, making it virtually immune to remote hacking.
Think of it like this: a hot wallet is the cash in your pocket, and a cold wallet is your savings locked away in a bank vault. For any amount of crypto you can't afford to lose, a hardware wallet from a trusted brand like Ledger or Trezor isn't just a good idea—it's essential.
Crucial Takeaway: A hardware wallet is the single best investment you can make in your digital asset security. By keeping your private keys completely offline, it creates an impenetrable barrier between your funds and online attackers.
Recognizing Modern Scam Tactics
Scammers are always evolving their game. They've moved way beyond simple fake giveaways and are now running sophisticated psychological operations designed to trick even savvy users. You have to learn to spot their new playbook.
Here are a couple of the most common schemes I see:
- Phishing Attacks: These usually show up as an email or DM that looks like it's from a legitimate exchange, wallet provider, or DeFi platform. They'll create a sense of urgency, telling you to "verify your account" or "claim a reward." The link they provide leads to a perfect clone of a real website, built for one purpose: to steal your login info or seed phrase.
- Pig Butchering Scams: This is a nasty, long-con investment fraud. The scammer spends weeks, sometimes months, building a personal relationship with you. Once they've earned your trust, they introduce you to a "secret" trading platform showing unbelievable returns. After you invest, they invent fees and taxes to milk you for more money before vanishing without a trace.
Always be skeptical. Unsolicited messages and promises of guaranteed high returns are massive red flags. If it sounds too good to be true, it absolutely is. Remember, the entry point for most of these scams is just one bad click. Good old-fashioned cybersecurity hygiene—like never, ever clicking suspicious links—is still your most powerful defense.
Got Questions? We've Got Answers
When you've been scammed, your head is probably swimming with questions. It's completely normal. Let's tackle some of the most common ones we hear from people in your exact situation.
Is It Actually Possible to Get My Stolen Crypto Back?
Let's be direct: it's possible, but there are no guarantees. The biggest factors are speed and the scam's sophistication. If you act fast, we can start tracing the funds before they disappear into a mixer or get scattered across dozens of wallets.
Getting law enforcement and a professional tracing service involved early dramatically boosts your chances. They have the tools to follow the digital breadcrumbs before the trail goes completely cold. For example, a recent case saw Thai authorities and private partners claw back $432,000 in stolen crypto precisely because they moved fast to trace and freeze the assets.
What's the Deal with Crypto Recovery Service Fees?
Any legitimate recovery service worth its salt will work on a contingency basis. This means they only get paid if you get paid. Their fee is a percentage of the funds they successfully recover. It’s a simple, honest model that aligns their interests with yours.
If a service demands a hefty upfront fee—especially if they want it in crypto—run. That’s the classic sign of a recovery scam, a nasty trick where scammers prey on victims a second time.
How Long Does This Whole Recovery Process Take?
There’s no single answer here. The timeline can be anything from a few weeks to several years, and it all depends on the complexity of your case.
A straightforward trace with a clear transaction path might get resolved relatively quickly. But if the funds have crossed international borders and we need to coordinate with multiple law enforcement agencies, you're looking at a much longer haul. Patience is key.
Can I Write Off Stolen Crypto on My Taxes?
This one's tricky and gets into some murky tax territory. The IRS has guidance suggesting you might be able to claim a theft loss, but typically only if the scam involved an investment you made for profit.
If your loss came from something personal, like a romance scam, it’s generally not deductible under current tax law. Your absolute best bet is to talk to a tax professional who actually understands the crypto space. They can give you advice tailored to your specific situation.
If your issue isn't a scam but a lost password or a compromised seed phrase, don't give up. Wallet Recovery AI uses sophisticated, AI-powered methods to get you back into your wallet securely. Find out how we can help and start your recovery today.


Leave a Reply