When you’re staring at a lost crypto wallet, the temptation to grab the first available "EZ file recovery" tool can be overwhelming. These generic programs scan a drive for any trace of deleted data, and on the surface, it sounds like a perfect solution.
But using one of these tools for a delicate crypto wallet is like using a bulldozer to find a fragile key in a warehouse—you might get lucky, but you're far more likely to crush the very thing you’re trying to save.
What Is EZ File Recovery And How Does It Work?

When you "delete" a file, your computer doesn't actually erase it. It just marks the physical space on the hard drive as "available for use." The data itself lingers, like a ghost in the machine, waiting to be overwritten by new information.
An EZ file recovery program scans these available spaces, hunting for recognizable file patterns.
Think of it as a librarian trying to piece together a shredded book. The software looks for file "signatures"—unique headers and footers that identify a file as a JPEG, a PDF, or a text document. Once it finds a matching start and end, it grabs everything in between and calls it "recovered."
This process is completely generic. The software doesn't know what it's recovering; it only recognizes basic file types. It treats a complex, encrypted crypto wallet with the same blunt force as a deleted cat meme.
This works surprisingly well for simple, small files like a single picture. The process fails, however, when files are complex or were stored in multiple pieces (fragmented) across the drive.
The Problem With Crypto Wallet Files
A cryptocurrency wallet file, like a wallet.dat or a JSON keystore, isn't just a simple document. It’s a highly structured, precisely encrypted database that holds your private keys. The integrity of this file is absolute—even one byte out of place can make it completely worthless.
Generic EZ file recovery software is blind to this critical need for precision. It operates with a few dangerous assumptions:
- It assumes a standard file structure. The tool looks for a generic start and end signature, grabbing the data in between. It has no specialized awareness of the unique, often proprietary structures used by wallets like MetaMask or Electrum.
- It can't reassemble fragmented data. If your wallet file was stored in several non-contiguous blocks on the drive, a generic tool might only find one piece or stitch them together in the wrong order, creating a corrupt and unusable file.
- It offers zero verification. The software might present you with a "recovered" file, but it has no way to confirm if that file is intact or hopelessly broken. You’re left to find out the hard way, often after the tool has overwritten the original data fragments during the "recovery" process itself.
Quick Answer: Can EZ File Recovery Safely Recover Crypto Wallets?
Before you run any generic tool, it's crucial to understand the trade-offs. Here’s a direct comparison of the risks versus the potential benefits when dealing with something as valuable as a crypto wallet.
| Aspect | EZ File Recovery Tools | Specialized Recovery Services |
|---|---|---|
| Approach | Generic, brute-force scan for all file types. | Targeted, wallet-specific algorithms. |
| Data Integrity | High risk of partial or corrupt recovery. | Focuses on preserving file structure and integrity. |
| Verification | None. Cannot confirm if a recovered wallet is valid. | Includes steps to validate the integrity of the recovered file. |
| Safety | High risk of overwriting the very data you need to recover. | Uses safe, non-destructive methods on cloned drives. |
| Best For | Simple, non-critical files like photos or documents. | Complex, high-value files like encrypted crypto wallets. |
This lack of specialized understanding is precisely why using a standard EZ file recovery tool is a high-stakes gamble. It’s an approach that prioritizes finding anything over correctly recovering the one thing that matters. That distinction is everything when the file you’re trying to save holds the keys to your assets.
The Critical Risks of Using Generic File Recovery for Crypto

I get it. When you think you’ve lost access to your crypto, grabbing a generic ez file recovery tool feels like a lifeline. But I have to warn you, it’s often the worst thing you can do. These programs are generalists, designed to find deleted photos and documents—not highly sensitive, complex wallet files.
Using one of these tools for a crypto wallet is like trying to perform microsurgery with a sledgehammer. You’re far more likely to cause irreversible damage than you are to succeed. At the root of the problem, these tools simply don’t understand the fragile structure of a wallet file. They see random data, not irreplaceable value, leading to several huge risks.
The Danger of Partial File Restoration
The single biggest risk is turning a recoverable file into a permanently corrupted one. An ez file recovery program might find pieces of your deleted wallet, but it often has no idea how to put them back together in the correct order.
For a Word document, this might mean a few garbled sentences. For a crypto wallet like a wallet.dat file, it's a complete disaster. A wallet is a precise database where every single byte matters. If the recovery tool stitches the fragments together incorrectly, you end up with a file that looks recovered but is actually worthless.
The real tragedy here is that this botched recovery attempt can overwrite the original, recoverable data fragments on your drive. The "restored" but now-corrupt file takes the place of the very pieces a professional could have used, completely destroying any real chance of getting your funds back.
This is a one-way street. Once that original data is gone, it’s gone forever. No software in the world can undo the damage.
Hidden Malware and Spyware Threats
Many so-called “free” recovery tools have a nasty hidden cost. To make money, some developers bundle their software with adware, spyware, or even outright malware. You download the program thinking you’re getting help, but you’re actually installing a thief on your own computer.
This creates a terrifying scenario. If the tool does manage to restore your wallet file, the spyware hiding inside could be designed to:
- Log your keystrokes to steal your password the moment you type it.
- Scan your hard drive for any file named
wallet.datand send it to the attacker. - Monitor your clipboard to grab your seed phrase if you copy and paste it.
Your desperate attempt to recover your crypto just became an open invitation for someone to steal it. The very tool you trusted to help could be the thing that drains your account. If you want to see just how different these tools can be, we've broken down some of the most common options. See our detailed comparison of data recovery tools.
Privacy Risks and Data Exposure
Even when a recovery program isn't intentionally malicious, it can still create a massive privacy headache. Some apps will upload file fragments or system data to their own servers for "analysis" without clearly telling you. They might frame it as part of a "deep scan" feature.
For a normal picture, that’s a privacy violation. For a crypto wallet, it’s a five-alarm security breach. You have absolutely no idea:
- Where your data is going.
- How securely it’s being stored.
- Who has access to it.
- Whether it will ever be deleted.
Uploading even pieces of a wallet.dat or a JSON keystore file to an unknown third party is a massive gamble. You’re betting your financial security on the ethics and competence of a faceless company.
The stakes here are incredibly high. The need for specialized, trustworthy services has never been greater, especially as people lose access to significant holdings. The right professional approach makes all the difference.
When You Absolutely Need a Professional Recovery Service

We get it. The temptation to download a quick-fix tool and solve the problem yourself is huge. But there are moments when going the DIY route with a generic program is the worst thing you can do. Knowing when to stop and call in an expert is often the single biggest factor in whether you’ll ever see your crypto again.
Think of it this way: every failed recovery attempt with a basic tool can shred your wallet's data even further. It’s like trying to reassemble a torn-up photo. The more you handle the pieces, the more you smudge the image and fray the edges, making it impossible for even a specialist to put it back together.
Some situations are giant, flashing red flags. If you see one of these, you need to step away from the keyboard and get professional help immediately. These aren't just suggestions—they are critical warnings.
Physical Hard Drive Damage
This is the big one. If your drive is making any strange clicking, grinding, or buzzing noises, that's a sign of mechanical failure. The platters inside, which hold your wallet file, are literally scraping themselves into dust.
Warning: Running any software on a physically failing drive, especially a resource-heavy tool like ez file recovery, is like trying to run a marathon on a broken leg. You will cause permanent, unfixable damage. Power the drive down now.
A professional service uses a specialized "clean room" to physically disassemble the drive and painstakingly extract the data. This is a delicate hardware surgery, something no piece of software can ever perform.
Lost Password and Encrypted Wallet
Losing the password to an encrypted wallet is bad enough. But if the wallet file itself is also missing or corrupted, the problem just became ten times harder.
A generic file recovery tool is completely out of its depth here. Even if it manages to find your wallet.dat file, you still just have a locked digital box. You're now fighting a war on two fronts:
- File Recovery: The wallet file needs to be perfectly pieced back together from scattered fragments on the drive.
- Password Cracking: That recovered file then needs to be hit with advanced brute-force attacks to find the password.
This requires a unique set of algorithms that can first ensure the file is intact and then begin the decryption process. This is a dual-pronged attack that no off-the-shelf software is built for.
Obsolete and Unsupported Wallets
What if your wallet file is a relic from the past? We're talking about old software like MultiBit, early versions of Jaxx Liberty, or obscure altcoin wallets from 2017 that have long since been abandoned.
These are ticking time bombs for a few reasons:
- Unique File Structures: Many old wallets used weird, proprietary file formats that modern recovery tools simply don't recognize.
- Compatibility Issues: The original wallet software might not even run on a modern computer, so you can't open the file even if you recover it.
- Poor Documentation: How these wallets handled keys and encryption is often a mystery, requiring a specialist to basically reverse-engineer the entire thing.
Trying to use ez file recovery on these files is a complete shot in the dark. An expert, on the other hand, has seen these cases before and often maintains a library of old software and a deep understanding of these forgotten formats. To see how we tackle these unique challenges, take a look at our dedicated wallet recovery service.
In complex cases involving everything from hardware failure to stolen funds from wallets like MetaMask and Electrum, expert intervention is becoming the gold standard. As a sign of what's possible, leading firms in the space now report success rates as high as 98% in some scenarios, with one group, Cipher Rescue Chain (CRC), having recovered over $830 million in assets by 2026. This shows just how powerful specialized expertise can be when things go seriously wrong.
Safer Steps if You Must Attempt Basic Data Recovery
We get it. The feeling of panic when a crypto wallet file vanishes can make you want to try anything to get it back, right now. While our official advice is always to avoid DIY recovery for something this critical, we also know that sometimes people need to act.
So, think of this as a harm-reduction guide. The goal here isn't a miraculous recovery—it's to stop you from accidentally turning a recoverable problem into a permanent, catastrophic loss. You're applying first aid, not performing surgery. Every step is about preserving the fragile data fragments on the drive before a professional can take over. One wrong move, and it's game over.
The Golden Rule: Stop Using the Drive
This is the most important step, and it's not optional. The second you notice the file is gone, stop everything. If it’s your main computer, shut it down. Immediately.
Every moment your computer stays on, it's writing data—log files, browser cache, system updates. Each tiny write operation could land on the exact spot where your "deleted" wallet file is waiting to be recovered. Continuing to use the drive is like trampling through a crime scene; you're destroying the very evidence you need.
Create a Perfect Clone of the Drive
Before you even dream of running a tool like EZ file recovery, you have to make a disk image. This isn't just copying files. A clone, or disk image, is a perfect, bit-for-bit replica of the entire drive, including all the "empty" space where your lost wallet file is hiding.
Working from a clone is absolutely essential for two reasons:
- It’s Your Safety Net: If the recovery software fails, corrupts the clone, or just doesn't work, you still have the original, untouched drive. You can then try a different approach or hand it over to a professional service.
- It Prevents More Damage: Running recovery tools directly on the affected drive is incredibly risky. The recovery process itself can write data, overwriting the file you're trying to save. By working on the clone, the original drive stays safe and isolated from harm.
A disk image requires special software. You're not dragging and dropping files. Tools like
ddon Linux/macOS or other dedicated imaging programs create this perfect replica. This is your only undo button. Without it, you get no second chances.
Use a Separate Computer for the Recovery
Never, ever install recovery software on the same drive you're trying to recover from. This is the cardinal sin of data recovery. The installation alone writes hundreds, if not thousands, of new files, almost guaranteeing it will overwrite the data you're desperate to find.
The proper way to do this is to connect your cloned drive to a completely different, trusted computer. All the work—installing software, running scans, and attempting the recovery—happens on this second machine. This ensures the target drive is only being read from, never written to.
Test Software in a Sandbox First
The internet is full of "free" EZ file recovery programs, but many are traps. They come bundled with malware, spyware, or keyloggers designed to steal the very crypto you’re trying to recover.
Before you run any downloaded tool, you have to test it in a "sandbox." A virtual machine (VM) is perfect for this. It’s an isolated digital computer running on your real one. Install the recovery tool inside the VM and watch what it does. Does it try to connect to the internet? Install junk you didn't ask for? If anything looks suspicious, delete the entire VM. It’s not worth risking your assets.
This flowchart shows where DIY attempts end and professional intervention becomes the only viable path.
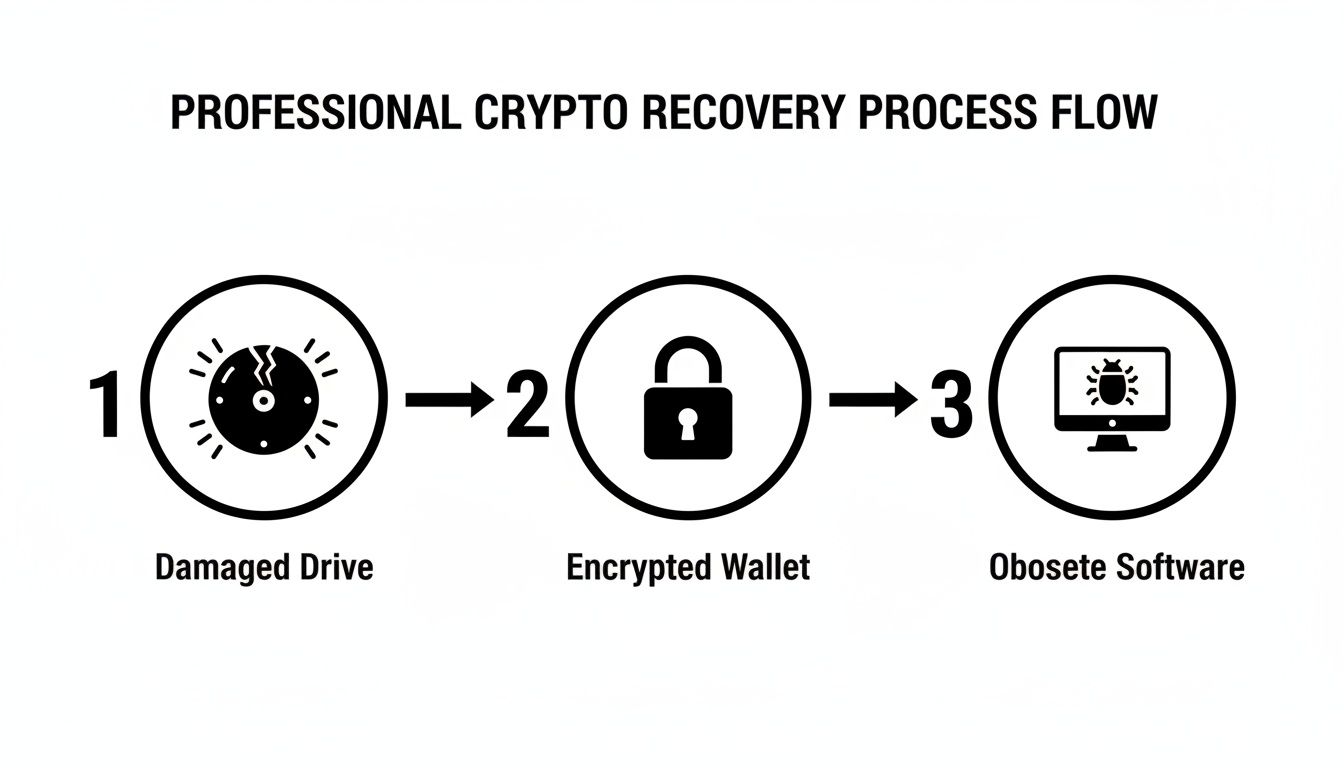
As you can see, problems like physical drive damage, complex encryption, or old, unsupported wallet software are far beyond what a simple tool can handle. Following the steps above gives you the best shot at not making things worse.
How a Specialized Crypto Recovery Service Works
When an ez file recovery tool fails, it's typically because the problem requires more than a simple scan. A specialized crypto recovery service moves beyond guesswork and applies deep, domain-specific expertise. Think of it as the difference between a blunt instrument and a surgical tool.
Generic software sees a corrupted file as a meaningless jumble of data. A professional service like Wallet Recovery AI, on the other hand, is trained to recognize the specific digital fingerprints of wallet files. We don't just find a file named wallet.dat—we understand its internal structure, how it encrypts private keys, and how it was designed to communicate with its native blockchain. This fundamental knowledge is the core of our entire recovery process.
The Initial Secure Consultation
Our work doesn't start with software; it starts with a conversation. The first step is always a secure, confidential consultation to understand exactly what happened. We need to know every detail: the wallet type, how the data was lost, any previous recovery attempts you've made, and any scraps of information you might recall.
This initial assessment is crucial. It lets our specialists build a precise profile of the problem and determine the nature of the data loss. It’s the difference between a doctor asking for your symptoms before making a diagnosis and a tool that just starts operating blind.
We prioritize your privacy from the moment you contact us. All communications are encrypted, and our entire process is built on strict non-disclosure and security protocols to keep your sensitive information protected.
Based on this consultation, we map out the most probable path to a successful recovery and give you a transparent overview of the steps we’ll take. We don't make blanket promises—we build a specific strategy based on the facts of your case.
Proprietary Algorithms and Targeted Analysis
This is where our specialized approach really comes into play. Unlike a one-size-fits-all program like ez file recovery, we use proprietary algorithms built specifically for different wallet technologies. Our software is engineered to:
- Recognize Unique Wallet Signatures: We can identify files from a huge range of wallets, including Bitcoin, Ethereum, and hardware wallet backups from Ledger and Trezor, even if the files are damaged or incomplete.
- Intelligently Reconstruct Files: If your wallet file has been fragmented or partially overwritten, our tools use advanced logic to piece it back together, preserving its critical cryptographic structure.
- Analyze Data Fragments: Our systems can find and interpret fragments of seed phrases or private keys scattered across a drive's unallocated space—something a generic tool would completely miss.
It's like trying to reassemble a shredded document. A standard tool just tapes pieces together at random. We act as an expert who knows the original document by heart, carefully matching every tear and fiber to restore it perfectly. This meticulous work is the only way to ensure the recovered file is not just found, but fully functional.
The need for this kind of expert help is clear. The industry is grappling with massive challenges, from user error to illicit flows that Chainalysis estimates topped $158 billion. In the middle of this, 2025 data from Crypto Recovers showed that over $2.5 million was successfully restored from wallets thought to be lost forever, including a single recovery worth $1.5 million. This reflects a broader crisis where, despite 30% US crypto ownership in 2026, 21% of owners have suffered net losses, many due to losing access to non-custodial wallets. You can find more about these statistics on the massive challenge of recovering digital assets.
The Recovery and Verification Phase
Once our algorithms locate and rebuild the potential wallet data, our job isn't done. The final, critical phase is verification. We use a secure, air-gapped offline environment to test the integrity of the recovered file. This might involve trying to decrypt the wallet with password fragments you provided or checking it against a testnet to confirm it contains the correct public addresses.
We only consider a recovery successful after we have confirmed we have a working, accessible wallet. This last step gives you complete assurance that the file you get back isn't just a collection of data, but the verified key to your funds.
Your Top Questions About Crypto Wallet Recovery, Answered
Losing access to a crypto wallet is incredibly stressful, and it's natural to have a lot of urgent questions. We see people in this situation every day. This section is designed to give you clear, straightforward answers about the real risks of using generic tools like ez file recovery and what the safest next steps actually are.
Can an EZ File Recovery Tool Find My Lost Seed Phrase?
This is probably the most common question we get, and the answer is almost always no. A seed phrase isn't stored on your computer as a single file, like a Word document or a photo that a recovery tool can easily spot.
It's a mnemonic phrase that you're meant to write down and keep offline. Trying to find it with a file recovery tool is like searching a hard drive for a conversation you had out loud—the tool is looking for a specific file type that simply doesn't exist in that format. Any fragments of data containing those words would be scattered and unrecognizable to standard software.
Is a Paid File Recovery Program Safer Than a Free One?
While a paid, premium file recovery tool is less likely to be loaded with malware than a random "free" program, it is not any safer for recovering a crypto wallet. Both free and paid generic tools have the same critical flaw: they don't understand the unique, fragile structure of a wallet file.
Think of it this way: a free tool might be a rusty hammer, and a paid one is a brand-new, top-of-the-line hammer. But if you need to perform surgery, it doesn't matter how good the hammer is. It's the wrong tool for the job.
The real danger—incomplete recovery that permanently corrupts your wallet file—is exactly the same with both. Paying for a generic tool just gives you a false sense of security while you take the same catastrophic risk with your funds.
A paid program can't get around the basic limitations of its design. It still lacks the specialized protocols needed to correctly piece together fragmented wallet data, making it just as dangerous as any free tool.
What if My Wallet File Was on a Formatted Hard Drive?
If your wallet was on a drive that has been formatted, you absolutely must stop and avoid any DIY recovery attempt. Formatting a drive is like shredding a document into a million tiny pieces. The file system, which is the map that points to where all your data lives, gets completely erased.
An ez file recovery tool is now working blind with no map to follow. It might find random bits of data, but trying to reassemble them into a working wallet file without the original file structure is something generic software simply can't do.
This is a job for true digital forensics. A professional service uses highly specialized techniques to analyze the raw data on the drive platter itself, manually reconstructing the file. Any attempt you make with a DIY tool will almost certainly overwrite the faint data traces that are left, making even professional recovery impossible.
How Does a Professional Service Keep My Crypto Secure?
Reputable professional services operate with bank-level security because we understand exactly what’s at stake. Unlike a generic tool that might be sending data to unknown servers, an expert service is built on confidentiality and protection.
Here’s what that looks like in practice:
- Encrypted Communication: From your first contact with us to the final delivery of your files, every piece of communication is secured through encrypted channels.
- Non-Disclosure Agreements (NDAs): A legally binding NDA is standard procedure. It guarantees your case details and personal information are kept completely private.
- Secure, Offline Analysis: All recovery work is performed in a controlled, air-gapped environment. This means the systems are completely disconnected from the internet, eliminating any risk of online threats.
- Non-Destructive Process: Professionals work on a perfect, bit-for-bit clone of your drive, never the original. This ensures your original device is untouched and preserved.
These steps create a secure chain of custody, building a protective bubble around your data from start to finish.
When you're facing a lost crypto wallet, a DIY tool like ez file recovery is a gamble you just can't afford to take. For specialized, secure, and expert help, Wallet Recovery AI provides a clear path forward. Request a confidential consultation today to have an expert assess your situation and take the first safe step toward getting your assets back.

Leave a Reply