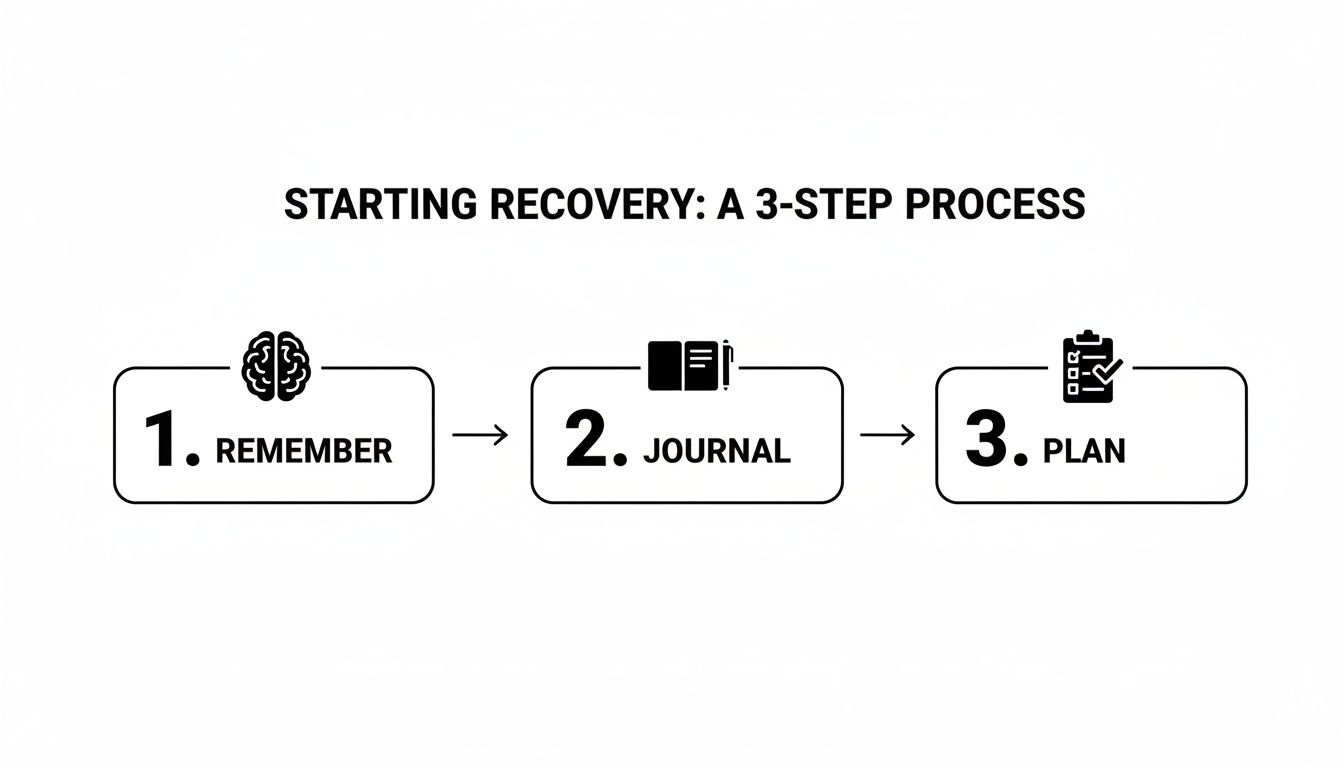
That sinking feeling is all too common. You remember stashing away some crypto years ago, but the login details are a complete blur. I've seen it countless times—what starts as a vague memory can turn into a serious treasure hunt. To have any chance of success, you need to turn that chaos into a methodical plan.
It all starts with what I call a 'recovery journal.' This is where you'll track every single clue, no matter how insignificant it seems right now.
Your Search for Forgotten Crypto Begins Here
Think back to the early, wild-west days of crypto. Many of us spun up wallets on a whim, maybe on an obscure platform, tossed in some coins, and then completely forgot about them. Fast forward to today, and that digital dust bunny could be worth a small fortune. The real challenge isn't just cracking a password; it’s about piecing together a puzzle you left for yourself years ago.
This isn't just a hypothetical scenario. The amount of value locked away in forgotten wallets is staggering. Just to give you an idea, in 2026 alone, our firm helped clients recover access to over $2.5 million in crypto. One of those recoveries was a single wallet worth about $1.5 million. Bitcoin made up roughly 70% of that total value. You can read more about these incredible crypto recovery stories and see how it’s done.
The Power of a Recovery Journal
Before you start frantically plugging old hard drives into your computer, just stop. Take a breath. The first move isn't a desperate search; it's organized reflection. We need to get you from "Where do I even begin?" to a clear, step-by-step strategy. This is why your recovery journal is the single most important tool you have.
This can be a simple notebook or a secure digital file—it doesn't matter. What matters is that it becomes your single source of truth, preventing you from running in circles and repeating the same dead-end searches.
Key Takeaway: A methodical approach is everything. Documenting every fragment of information, from a half-remembered password to the name of an old laptop, turns a chaotic search into a structured investigation.
Start by dumping everything you can possibly remember about the lost account onto the page. Don't filter or second-guess yourself. Every little detail is a potential breadcrumb.
- Wallet or Exchange Names: Did you use MetaMask, Electrum, Coinbase, or some other platform? Write them all down.
- Approximate Dates: When do you think you created the account? Try to tie it to a life event from that time—a new job, a move, a specific year in college.
- Email Addresses: This is a big one. List every single email you've used over the years. The creation email is often the master key.
- Old Devices: Make a note of any old computers, phones, or USB drives that might be gathering dust in a closet.
- Password Fragments: Jot down any common patterns, pet names, important dates, or phrases you used for passwords back then.
This initial brain dump is the foundation for your entire search. Once you have it all in one place, you can start to spot patterns and build a real plan of attack.
To get you started, here is a quick checklist of the essential information you should try to gather before diving any deeper.
Your Initial Recovery Checklist
| Information Category | What to Look For | Why It's Important |
|---|---|---|
| Account Identifiers | Wallet names, exchange platforms, public addresses | Narrows down which software or website you need to access. |
| Login Credentials | Old email addresses, usernames, password ideas | Essential for regaining access through standard recovery flows. |
| Timeframe Clues | Year of account creation, last known transaction date | Helps you filter through old emails and device backups efficiently. |
| Physical Hardware | Old laptops, external hard drives, USB sticks, written notes | These may contain the actual wallet files or seed phrase backups. |
Having this information organized from the very beginning will make the entire process much more manageable and increase your odds of a successful recovery.
Your Digital Treasure Hunt Starts Now
Alright, you’ve got your recovery journal ready. Now for the real work: digging through your digital past. Think of this less as a frantic search and more as a methodical excavation. Your crypto is almost certainly tied to an old device or an online account you've long forgotten.
We're going to go far beyond just typing "Bitcoin" into a search bar. The goal is to unearth the specific artifacts that can unlock your funds—things like wallet creation emails, transaction alerts, and the actual wallet files themselves. Patience is your best friend here.
This isn't just about random searching; it's about having a game plan. You'll start by jogging your memory, documenting everything you recall, and then building a clear strategy from there.
A structured approach, built on what you can remember and what you've written down, is the bedrock of a successful recovery.
Digging Through Your Email Archives
Your email account is a goldmine. Nearly every crypto service, whether it’s an exchange or a software wallet, sends a confirmation when you sign up. That single email can be the breakthrough, telling you exactly what service you used and when.
Forget simple keyword searches. We need to use advanced search operators to slice through the noise and find exactly what we're looking for. These let you filter by date, sender, and specific words in the subject line or body.
Let’s say you have a hunch you bought some crypto back in 2017. In a service like Gmail, your search could look something like this:"wallet" OR "bitcoin" OR "ethereum" OR "coinbase" before:2018-01-01 after:2016-12-31
This tells Gmail to only show messages with your keywords from that specific year. Tweak the dates and terms based on the notes in your journal.
Pro Tip: Don't skip the spam and trash folders. It was common for automated emails, especially from years back, to get filtered incorrectly. While some providers clear the trash after 30 days, it's always worth a look. You might just get lucky.
Try hunting for these specific phrases. They are far more likely to pop up in automated platform emails than just the name of a coin.
- "Welcome to"
- "Your new wallet"
- "Seed phrase" or "recovery phrase"
- "Confirm your email"
- "Transaction confirmation"
- "Deposit confirmed" or "Withdrawal successful"
Hunting Through Old Devices and Backups
In the early days, it was common to store wallet files right on the computer. That means your old laptops, desktops, and external drives are prime search locations. If you have old tech collecting dust, it's time to fire it up.
You aren’t looking for a file literally named “My Crypto Wallet.” Instead, you’re on the hunt for very specific file names and types that are hallmarks of popular wallet software.
Key Wallet Files to Look For:
wallet.dat: The classic. This is the file name used by the original Bitcoin Core wallet and many forks. Finding this is a huge win..json(Keystore files): Ethereum wallets like MyEtherWallet (MEW) often use this format, typically named something likeUTC--[timestamp]--[address].json. These files are encrypted with your password.- Default Electrum files: On Windows, check your
Users[Username]AppDataRoamingElectrumfolder. On macOS, look in~/.electrum. The default file is often nameddefault_wallet. - Text files (
.txt): A lot of people (against all advice) jotted down seed phrases or private keys in a simple text file. Search your entire drive for files containing terms like "seed," "phrase," "private key," or "12 words."
Check every piece of hardware on your list, from ancient laptops to USB sticks and external hard drives. Don't forget your cloud storage either. A quick search for "wallet," "seed," or "private key" inside your Google Drive or Dropbox might reveal a backed-up wallet.dat file or a text document with your recovery phrase. You never know what you might find in a long-forgotten folder.
Following the Money Trail on the Blockchain
Even if all you manage to dig up is a single, old public address, you’ve got a powerful breadcrumb. Every transaction on a public blockchain is recorded forever, creating a permanent, traceable history. This is where we stop rummaging through old files and start playing digital detective.
We’ll be using tools called blockchain explorers to follow the money.
Think of a blockchain explorer as a search engine for crypto. You pop in a public address, and it spits out every transaction ever linked to it. This public ledger is our roadmap, and learning how to read it can jog your memory and lead you right back to your forgotten funds.

The data you see here—where the crypto came from, where it went, and when—is the key to retracing your steps and finding other accounts you once controlled.
Decoding Your Transaction History
Let's say you find an old Ethereum address from 2018 in an email. The first thing you do is plug it into an explorer like Etherscan for Ethereum or Blockchain.com for Bitcoin. At first glance, you’ll just see a list of cryptic addresses and values, but if you look closely, patterns start to emerge.
Your main goal here is to spot transactions that went to an exchange. You might see a bunch of small, incoming transfers from who-knows-where—maybe from some early mining experiments or a freelance gig you forgot about. But then you spot it: a single, large outgoing transfer to an address with thousands of other transactions.
That’s a massive clue. Wallets with that much activity are almost always "hot wallets" belonging to major exchanges like Coinbase or Binance. Often, the explorer will even label the address with the exchange’s name if you click on it.
Pinpointing a transfer to an exchange is a huge win. It tells you exactly which platform you used, so you can stop hunting for a lost seed phrase and switch gears to the exchange's account recovery process. If you want a deeper look at these tools, you can learn more about what a blockchain explorer is and how it all works.
Tracing Transactions to Uncover Other Wallets
Beyond finding exchange accounts, your transaction history can lead you to other personal wallets you’ve completely forgotten about. Over the years, it was common to spin up multiple wallets for different reasons.
Here are a few tell-tale signs I always look for:
- Look for Round-Number Transfers: Did you send exactly 1.0 ETH or 0.05 BTC to another address? We tend to move funds between our own wallets in clean, round numbers, not the messy, hyper-specific amounts used for payments.
- Analyze Transaction Timestamps: If you spot a transaction to an unknown wallet on the same day you set up your main one, you might have been creating a backup or a separate "cold storage" wallet.
- Check for Small "Gas Fee" Transactions: Sometimes you’ll see a tiny amount of crypto sent to a brand-new wallet. This was often done just to give the new wallet enough gas to make its first transaction. These small, seemingly random transfers are strong indicators that you also control the destination address.
Every new address you identify as yours becomes another starting point. You can plug that address into the explorer and start the whole process over again, slowly mapping out a web of your past crypto activity. It’s a methodical approach, but it can turn one small clue into a complete picture of your forgotten assets.
Reconstructing Your Passwords and Seed Phrases
So you’ve found it—that old wallet.dat file or a long-forgotten keystore. That initial rush of excitement is real, but it’s often just the first step. Now comes the hard part: remembering the password or seed phrase that actually unlocks the funds. This is where a little bit of method, memory, and digital detective work all come together.

If you're staring at a locked wallet file, you're not alone. It's a common story in the crypto world. With nearly a third of Americans owning crypto, a staggering 21% report net losses, and a big chunk of that comes from simple access issues like a forgotten password. While many owners see great returns, those gains mean nothing if you can't get to them. A recent annual cryptocurrency consumer report dives deeper into these numbers, showing just how much value is trapped behind lost credentials.
Jogging Your Memory for Passwords
Your memory is the first place to look, but it rarely serves up a password on a silver platter. The trick is to give it the right cues. In your recovery journal, create a new section just for brainstorming password fragments. Don't just list random words; think about the patterns you used back when you created the wallet.
Try to put yourself back in that moment. What was going on in your life? A new job? A move to a new city? Maybe a new pet or relationship? We often embed little snapshots of our lives into our passwords without even realizing it.
Password Reconstruction Prompts:
- Base Words: Jot down any core words you loved to use—old nicknames, the street you grew up on, your favorite characters from a book or movie.
- Significant Numbers: Did you have a habit of adding a specific year, like your graduation year? What about an old apartment number or a lucky number?
- Special Characters: Were you a fan of ending passwords with an
!? Maybe you used$to replace the letter 's'? Document all these quirks. - Combinations: Think about your formula. Was it
[Word][Number]!or[Number]_[Word]? Try to map out the structure you typically followed.
Don't underestimate tiny variations. I've seen access come down to the difference between "Hunter2!" and "hunter2!". Be methodical and test everything—capitalization, number substitutions (
3for 'E'), and common special characters at the beginning or end.
This isn’t about random guessing; it's about building a list of potential ingredients and then systematically trying the combinations. It takes patience, but it’s far more effective. For a more detailed guide, check out our post on how to find old passwords.
Rebuilding a Partial Seed Phrase
A seed phrase (or recovery phrase) is a different beast entirely. If you've managed to find most of it—say, 10 out of 12 words, or even 23 out of 24—you are incredibly close to recovery.
Unlike a password, seed phrases aren't just random words. They come from a standardized list called the BIP-39 wordlist, which contains exactly 2,048 words. This predefined structure is a huge advantage for recovery.
Let's say you have 11 words of a 12-word phrase. That last word isn't random; it's a "checksum" word, mathematically derived from the first 11. With the right tools, you can instantly calculate the only possible word that completes the phrase.
What if a word is missing from the middle? The process becomes trying all 2,048 words from the BIP-39 list in that blank spot until the wallet's checksum validates. It's a brute-force approach, but it's a finite and achievable one.
If you have all the words but aren't sure of the order, the problem gets more complex, but it's often still solvable, especially for a 12-word phrase. Automated tools can test the permutations far faster than any human could. The key is to be systematic: write down every word you have, note which ones you're certain of, and let the software work through the rest.
You’ve torn apart old hard drives, followed transaction histories down rabbit holes, and tried every password you’ve ever used. But that wallet is still locked tight.
At some point, the search hits a wall. The technical challenges get steeper, or the amount of crypto at stake is just too high to risk making a mistake. This is when you should seriously consider calling in the experts.
Recognizing you’ve hit your limit isn’t admitting defeat. It’s a strategic move to give yourself the best possible shot at getting your funds back. Fumbling around with passwords can sometimes corrupt a file, and complex data issues are just not a DIY job.
When Your Best Efforts Just Aren't Enough
The methods we've walked through solve a lot of common lockout problems. But some situations really do require specialized tools and years of experience. If any of these sound familiar, getting professional help is probably your next move.
- Corrupted Wallet Files: You found the
wallet.dator.jsonfile, but it’s giving you an error and won’t open. This usually means the file is damaged. Professionals have forensic tools that can often piece together the corrupted data to pull out the private keys. - Partially Overwritten Data: You located a wallet file on a hard drive that’s been used for other things since. It's very possible that parts of that file have been overwritten by new data. Specialized data recovery can sometimes reconstruct the file from the fragments that are left.
- Complex Password Cracking: You have a vague memory of the password—maybe a few words or a pattern—but you can’t nail it down. Trying thousands of combinations by hand is impossible. A recovery service uses high-powered hardware to run through millions, or even billions, of targeted variations based on the clues you provide.
A Note from Experience: A lot of the early crypto wallets used quirky, non-standard encryption methods that are now totally obsolete. A true recovery specialist has seen these old formats before and has the specific software needed to crack them—stuff you just won’t find available for download online.
The amount of forgotten or lost crypto out there is staggering. Just to give you a sense of scale, research shows illicit crypto wallets took in $158 billion in 2025 alone. While that figure is about crime, it shows how much value is sitting in digital wallets. Legitimate owners are in the same boat, and professional services have a long history of successfully getting it back. You can see the full breakdown in the 2026 Crypto Crime Report.
How AI-Driven Recovery Works
Today’s best recovery services don't just rely on raw computing power; they use AI to make the search smarter. Instead of just guessing randomly, an AI model takes all your clues—old pet names, important dates, common phrases you use—and builds a targeted attack.
For instance, say you remember the password had your kid's name, a number, and a symbol. The AI won't just try "Fluffy123!". It will intelligently test "fluffy123!", "Fluffy!123", "FLUFFY-1-2-3", and countless other logical patterns built from your personal memory fragments. This focused approach dramatically speeds up the process and finds passwords that manual guessing would never get to.
How to Vet a Recovery Service
Handing over your wallet file means you need to trust the person on the other end. Do your homework, because not all "recovery experts" are who they say they are.
Here's what to look for in a trustworthy service:
- Fee Structure: A reputable firm, like Wallet Recovery AI, will always work on a success-based fee. You should never pay anything upfront for the recovery attempt. They only take a commission from the funds after you have regained access. If they ask for money first, walk away.
- Security and Privacy: The service must have airtight security. They should work under a strict non-disclosure agreement (NDA) and will never ask you to send your actual crypto to them. The entire process should be transparent and keep your information completely confidential.
- Reputation and Proof: Look for a proven track record. Find reviews, case studies, and real testimonials from previous clients. A history of successful recoveries, especially for your specific type of wallet, is the best signal you can get.
Deciding to bring in a professional is a big step. But if you know when to make the call and how to choose the right partner, you’re making the smartest possible decision to get that lost crypto back.
Common Questions About Crypto Account Recovery
When you're trying to track down old crypto, a lot of the same questions pop up. It’s easy to hit a wall and wonder if you’re even on the right track.
Let's clear the air and tackle the questions we hear every single day. Getting straight answers from the start can save you a ton of time and set realistic expectations.
Can I Really Recover a Wallet If I Lost Everything?
This is the big one, and the honest answer is: it depends on what you mean by "everything."
Look, if there's truly nothing—no access to old email accounts, no password ideas, no old hard drives in a box somewhere—then recovery is next to impossible. The digital trail has gone completely cold.
But that’s almost never the case. Most people who believe they've lost it all actually have a breadcrumb or two. A faint memory of the wallet's name, a partial password, an old laptop in the attic… these are powerful starting points.
A single clue is often enough to get started. A professional service excels at taking small, seemingly insignificant fragments of information and piecing the puzzle back together, turning a sliver of hope into tangible success.
The entire recovery process hinges on having at least one solid lead. Even if you only remember the year you bought the crypto, don't dismiss it. Write every single detail down in your recovery journal.
How Safe Is It to Use a Wallet Recovery Service?
Handing over potential access to your assets requires a huge amount of trust. Any reputable wallet recovery service understands this and puts your security above all else. Their entire business model depends on it.
A legitimate service will always operate under a strict non-disclosure agreement (NDA) to guarantee your privacy. The process should be transparent: you provide the clues, and they do the work in a secure, offline environment. They should never ask you to send them your actual crypto.
Once they succeed, they’ll coordinate the secure transfer of the funds with you and take a pre-agreed percentage as their success fee. If anyone asks for payment before the recovery is complete, that’s a massive red flag.
Always do your homework:
- Check their track record: Look for real-world testimonials and case studies.
- Verify the fee structure: They should only get paid if you get paid. A no-win, no-fee model is the standard for legitimate services.
- Confirm their security practices: Ask them exactly how they protect your files and information during the recovery attempt.
How Long Does the Crypto Recovery Process Take?
Patience is a virtue in crypto recovery. There's no fixed timeline, as the duration depends entirely on the clues you have and the complexity of the encryption.
A straightforward password search with good hints—like a solid base word and a few possible number patterns—could be wrapped up in just a few days.
On the other hand, more complex jobs take time. Brute-forcing a password with very few hints can take weeks or even months of non-stop computation. Recovering a wallet from a corrupted file might involve digital forensics that also stretches the timeline. A good service will give you a realistic estimate upfront and keep you in the loop.
What if My Wallet Is on a Defunct Platform?
This is a really common problem, especially for anyone who got into crypto early. You might have used a wallet like Jaxx or MultiBit Classic that has since been shut down, and now you think the funds are gone for good.
Here's the good news: that's usually not the case.
The critical data—your private keys or seed phrase—is still inside those old wallet files (wallet.dat, .json, etc.). Those keys are what grant access to your funds on the blockchain itself, and they are still valid, no matter what happened to the original software.
The real challenge is getting those keys out of an outdated and unsupported file. The methods for searching old devices we've discussed are still your best bet. If you find a wallet file but can't open it with any modern software, that’s the perfect time to call in a professional. They have the experience and custom tools needed to crack open these obsolete formats.
Feeling overwhelmed or stuck? You don't have to go it alone. The experts at Wallet Recovery AI specialize in turning these complex challenges into successful recoveries. Using advanced AI and a secure, success-based model, we help people find old accounts and get their crypto back. Contact us today for a confidential consultation.


Leave a Reply