That gut-wrenching moment you realize your crypto is gone is something I wouldn't wish on anyone. It’s paralyzing. But what you do in the next 30 minutes can make all the difference. The first moves are all about damage control and evidence gathering, turning your initial shock into focused action.
My Crypto Is Gone—What Do I Do Right Now?
Panic is the first emotion to hit. That’s normal. But you have to push past it and act methodically. The moments immediately following a theft are chaotic, but they're also when you have the most leverage to contain the situation.
Think of it as financial first aid. Your goal is to stop the bleeding and gather the digital clues left behind. It’s not just about the money; it's about seizing back control from whoever violated your accounts.
First, Isolate the Compromised Device
Before you do anything else, cut the attacker’s connection. If you even suspect your computer or phone has been compromised, get it offline. Now.
Unplug the ethernet cable. Turn off your Wi-Fi and cellular data. This simple act can sever a hacker's remote access, stopping them from grabbing more assets or digging deeper into your system.
Crucially, do not shut the device down. Turning it off can wipe the volatile memory (RAM), which might hold critical forensic clues about how the attack happened. Just get it off the network.
Second, Verify the Transaction on a Block Explorer
Now you need to confirm what happened. Grab a separate, trusted device—a different computer or your phone if you think your desktop was the target—and pull up a block explorer.
You'll need your public wallet address. Paste it into the explorer to see every transaction ever associated with it.
A block explorer is basically a public search engine for the blockchain. It lets you see exactly where funds went, confirm transaction details, and track their path in real-time. It’s an indispensable tool in these situations.
Look for the transaction you didn't authorize. If you see it, you have confirmation of the theft. This step gives you the first hard evidence you'll need for everything that comes next. For a deeper dive, our guide on what is a blockchain explorer breaks it all down.
Third, Gather the Critical Details
From the block explorer, you need to document everything meticulously. Don't rely on memory—copy and paste this information into a secure note.
- The Thief's Wallet Address: This is where your funds were sent. It's the most important piece of the puzzle for any tracing effort.
- The Transaction ID (Hash): This is the unique, unchangeable receipt for the transaction on the blockchain.
- Exact Timestamps: Note the precise date and time of the transaction.
- The Amount Stolen: Record the exact amount of each coin or token taken.
This information is the foundation for any report you'll file, whether it’s with an exchange, a tracing firm, or law enforcement.
To give you a sense of scale, crypto theft is a massive problem. In 2025 alone, hackers stole a staggering $3.4 billion globally, impacting at least 80,000 individual wallet holders.
The detailed 2026 crypto hacking report from Chainalysis shows that while huge exchange hacks make the news, tens of thousands of people just like you are the primary targets. By following these initial steps, you're doing everything right to set yourself up for the best possible outcome.
The first few minutes are a blur of adrenaline and fear, but a clear checklist can keep you grounded. Here’s a quick reference table for those critical first actions.
Immediate Actions for Suspected Crypto Theft
| Action Step | Why It's Critical | Example Scenario |
|---|---|---|
| Disconnect from Internet | Stops any ongoing remote access and prevents further losses from the same device. | You notice a strange transaction and immediately turn off Wi-Fi on your laptop, cutting off a hacker who was still exploring your files. |
| Verify on Block Explorer | Provides definitive proof of the theft and the exact trail of the funds. | Using your phone, you enter your wallet address on Etherscan and see 2 ETH being sent to an unknown address 10 minutes ago. |
| Document All Details | Creates an evidence log (transaction hash, thief's address, timestamp) for reporting. | You copy the transaction ID and the destination address into a secure document before contacting your exchange's support team. |
Following this simple three-step process won't magically bring your funds back, but it's the strongest possible start you can give yourself. It's about taking immediate, decisive action to contain the threat and prepare for the next phase: recovery.
Navigating Different Wallet Recovery Scenarios
The way you get your crypto back depends entirely on how you lost it. Losing a seed phrase is a totally different ballgame than dealing with a corrupted wallet file, and your recovery strategy has to match the problem.
Think of it like this: each wallet type—software, hardware, even an old paper wallet—has its own security model and, therefore, its own unique points of failure. The trick is to correctly diagnose the issue so you can apply the right fix. What feels like a dead end is often just a puzzle waiting for the right key.
This flowchart can help you map out your first moves, whether you’re sure it’s a theft or you just can’t seem to find your funds.
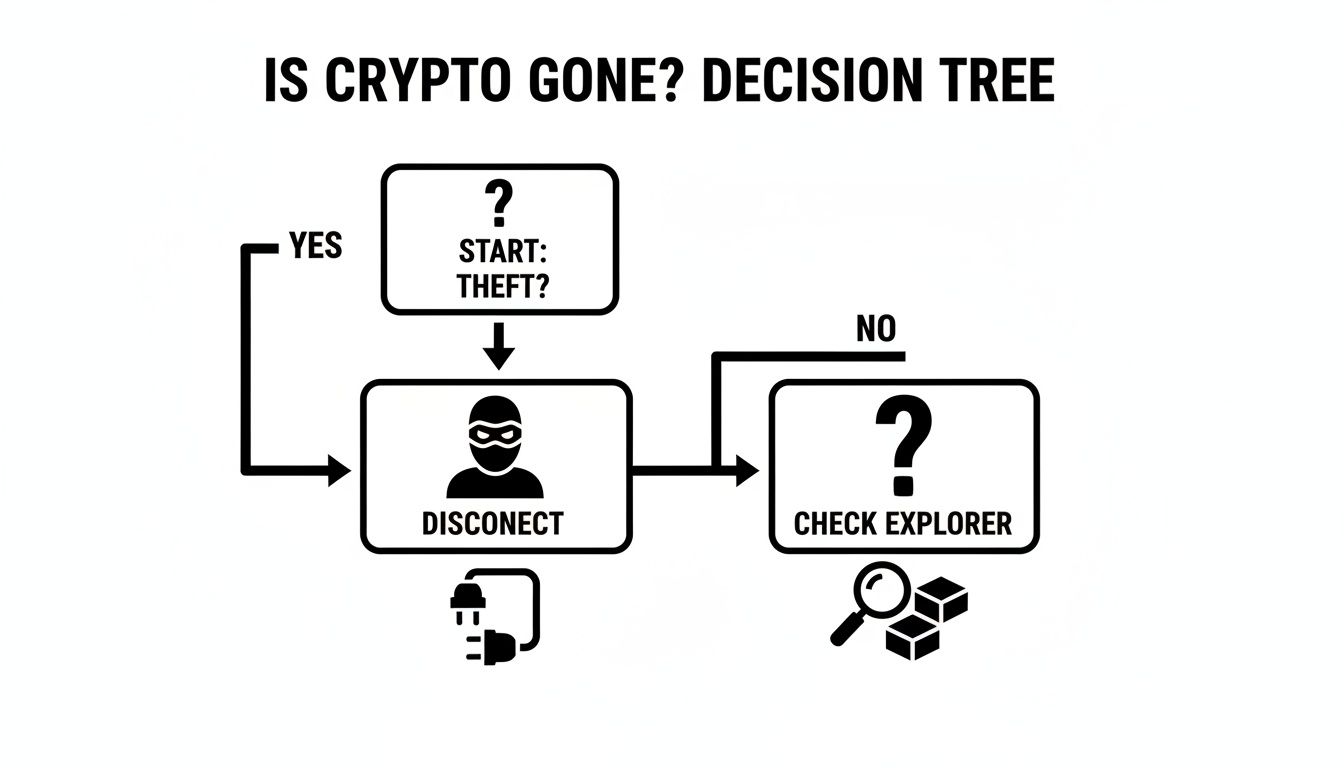
As you can see, if you suspect theft, the immediate priority is damage control. If you think you've just misplaced your crypto, your first stop should be a block explorer to verify what's really going on.
Software Wallet Recovery Methods
Let's talk about software wallets like MetaMask, Exodus, or Trust Wallet. They're incredibly convenient, but that convenience comes with specific risks. The two most common nightmares are forgetting your password or, much worse, losing your seed phrase.
If you just forgot the password, take a deep breath. You're not completely locked out. Most software wallets let you restore everything using your 12 or 24-word seed phrase. You’ll usually just need to reinstall the app and find the "Import" or "Restore from Seed Phrase" option. Simple.
But what if the seed phrase itself is gone? That's a five-alarm fire. Without that phrase, standard recovery methods are off the table. This is where you might need to call in the pros. Specialists can sometimes use forensic techniques to pull wallet files from your device, but only if the data hasn't been completely overwritten.
Your Seed Phrase is Everything.
With software wallets, the password just protects the app on your device. The seed phrase is the wallet. Guard it like it’s a block of gold and never, ever store it as a digital file.
Hardware Wallet Recovery Challenges
Hardware wallets from companies like Ledger and Trezor are the gold standard for a reason—they keep your private keys totally offline. Because of this, recovery almost always comes down to one thing: your 24-word recovery seed.
If your device gets lost, stolen, or smashed to bits, the fix is surprisingly easy. Just buy a new one (it can even be from a different compatible brand) and use your recovery seed to restore it. Your crypto was never on the device; it's on the blockchain. The seed is just your key to access it.
The real disaster strikes when you lose that seed phrase. Your options get very narrow, very fast.
- If you still have the device and your PIN: Don't wait. Immediately create a brand new wallet with a new seed phrase, write it down somewhere safe, and transfer every last asset over.
- If you've lost both the device and the seed phrase: I'm sorry to say it, but your funds are almost certainly gone for good. This is the brutal reality of self-custody. It’s why managing your seed phrase is the most important job you have.
Corrupted Files and Keystore Issues
Remember the old days? For wallets like MyEtherWallet or some of the original desktop clients, you might have used a keystore file (a JSON file) along with a password. This file is just your encrypted private key.
If that file gets lost or corrupted, things can get tricky.
- Hunt for Backups: The very first thing to do is scour every device, cloud account, and old USB drive you own for a copy of that keystore file.
- Try to Repair It: In very rare cases, a partially corrupted file can be salvaged with specialized tools, but don't get your hopes up. It's a long shot.
- Use Your Seed Phrase (If You Have It): If you were smart enough to also back up a seed phrase when you created the wallet, you can use that to bypass the keystore file completely. This is your best-case scenario.
In the end, every recovery attempt boils down to what information you still have. Whether it's a seed phrase, a private key, or a wallet file, that single piece of data is where any path to getting your crypto back begins.
When It's Time to Call in the Pros
At some point, you might hit a wall. Trying to recover stolen crypto on your own, especially after a direct theft, can feel like shouting into the void. This isn't the end of the road, though. A structured escalation plan is your next move, and knowing when to bring in exchanges, tracing firms, or law enforcement isn't admitting defeat—it's getting strategic.
The key is recognizing that moment. If your funds were drained from a centralized exchange account or you can see a clear transaction trail leading to a known service, it’s time to escalate. Immediately. These organizations have resources, legal teams, and investigative tools that you just don't have access to.
Your First Call: The Crypto Exchange
If the theft happened on a platform like Coinbase, Binance, or Kraken, your first official report goes directly to their support team. Don't just fire off a panicked email. Be methodical.
Open a support ticket and arm them with every piece of evidence you've gathered. This is your chance to give their security team a fighting chance.
- Transaction Hashes (IDs): The exact identifiers for every unauthorized withdrawal.
- The Thief's Wallet Address: The destination address that received your funds.
- Precise Timestamps: Every login alert, withdrawal confirmation, and suspicious activity.
- Screenshots: Any phishing emails, fraudulent messages, or unusual login alerts.
Keep your communication clear and to the point. State plainly that your account was compromised and funds were stolen. Their internal teams can immediately check if the thief's wallet is tied to another known account on their platform or a partner exchange. They can’t reverse a transaction, but they absolutely can freeze accounts and cooperate with the police.
A Quick Reality Check
Exchanges have their limits. They can lock an account if the stolen funds are somehow still sitting there, but that’s rare. Most criminals move assets off-platform within minutes. Still, your report creates an official paper trail, which is absolutely critical for everything that comes next.
Working with Professional Crypto Tracing Firms
Once your funds move off an exchange and disappear into a maze of unknown wallets, a professional tracing firm becomes your best hope. Think of them as digital bloodhounds. These specialists use advanced blockchain analysis to follow the breadcrumbs the thief left behind.
They can de-anonymize transactions, pinpoint when stolen funds hit another exchange to be cashed out, and compile a detailed forensic report. This report is often the exact piece of evidence law enforcement needs to issue subpoenas and uncover the real-world identity behind the thief's account. Choosing the right partner here is everything. You need a reputable cryptocurrency recovery firm with a transparent process and a proven history of success.
The crypto crime landscape is grim, but recovery is far from impossible. Coordinated efforts between law enforcement and these specialized firms are leading to major wins. While personal wallet attacks skyrocketed to 158,000 cases, successes like Interpol's Operation HAECHI VI—which reclaimed a staggering $439 million—prove that a structured approach works. The detailed 2025 crypto crime report from DeepStrike.io drives this point home: criminals are getting smarter, but so are the people hunting them.
Getting Law Enforcement Involved
Filing a police report can feel like a long shot, but it is an absolutely non-negotiable step. It officially documents the crime, which is a requirement for exchanges, banks, and courts to take any action on your behalf.
This screenshot from INTERPOL’s cybercrime division shows just how seriously global authorities are taking digital theft.
Your local police department might not be filled with blockchain experts, but they are your gateway to larger agencies that are. Your report can get escalated to the FBI or even INTERPOL, both of which have dedicated cybercrime units.
When you go to file your report, show up prepared with a complete evidence package.
- A clear, chronological story of what happened.
- All the transaction details and wallet addresses you've already collected.
- Copies of your communication with the crypto exchange.
- The forensic report from your tracing firm, if you have one.
The more organized you are, the more seriously they will take your case. Every report filed helps authorities spot patterns, connect dots, and link your case to larger criminal rings. The wheels of justice may turn slowly, but your official report is what gets them moving in the first place.
Building Your Case by Documenting Everything
When your crypto is gone, the single most powerful tool you have is evidence. I've seen countless recovery attempts stall because the victim's information was a jumbled mess. After the initial shock wears off, your number one job is to become a detective for your own case.
You need to build a clear, chronological case file. This isn't just about scribbling notes; it's about creating an organized story that anyone—from a support agent at an exchange to a federal investigator—can grasp immediately. This documentation is the foundation of any chance you have at recovery.

Think of yourself as the lead investigator at a crime scene. Every tiny detail matters.
Your Essential Evidence Checklist
Grab a dedicated notebook or start a secure digital document and just start dumping every piece of information you can think of. Leave no stone unturned.
- Transaction Hashes (TxIDs): For every single unauthorized transaction, copy the full hash. This is the non-negotiable proof of the crime on the blockchain.
- Wallet Addresses: Write down your wallet address (the one the funds were stolen from) and, crucially, the thief's receiving address. Use a block explorer to follow the money and note every address it hops to.
- Exact Dates and Timestamps: Log the precise time of the theft, making sure to include your time zone. Don't forget to note any related events, like suspicious login alerts or odd emails you received around the same time.
- Amounts and Types of Crypto: Get specific. Don't just say "some Bitcoin and ETH." Write down exactly 1.5 BTC, 10.2 ETH, and 5,000 USDT.
- IP Addresses and Device Info: Did you get a login notification from your exchange? It probably included an IP address and device details (e.g., "Login from Chrome on Windows from Seoul, South Korea"). Record this info.
This data is the technical backbone of your case. It’s the raw, undeniable proof of what happened and where your assets went.
Preserving Communication and Digital Clues
The blockchain tells half the story. The other half is how the thief got to you in the first place, which is absolutely critical in social engineering or phishing attacks.
Create a Timeline of Events
Start from the very beginning. When did you first click that weird link? When did you start talking to that "support agent" on Telegram? What file did you download? A clear timeline provides context that transaction data alone can't. It helps investigators understand the how and why.
From here, it's all about screenshots. Capture everything.
- Phishing Emails or Websites: Screenshot the full page, making sure the URL is visible. If you can, find out how to show the email's headers and grab a shot of that, too.
- Direct Messages: Get screenshots of the entire conversation on platforms like Telegram, Discord, or X (formerly Twitter).
- Malicious Software: If you were tricked into downloading something, note its name and where you got it. Do not open it again.
A quick pro-tip: take these screenshots from a separate, clean device. If your main computer is compromised, use your phone to take a picture of the screen. The goal is to preserve evidence without infecting your other gear. Your thoroughness at this stage directly impacts your chances of a successful outcome.
How to Spot and Avoid Recovery Scams

In the minutes and hours after you realize your crypto is gone, your judgment is clouded by panic and desperation. Scammers absolutely thrive on this. They swarm social media and direct messages, posing as "recovery experts" who promise to make everything right.
Their real goal is simple: to make you a victim for a second time. Learning to spot their tactics is just as important as trying to trace your stolen assets. This is about protecting yourself when you're most vulnerable.
Common Red Flags of a Recovery Scam
These predators follow a depressingly familiar script. If you're looking for help and run into any of these, it's time to walk away—fast.
- Guarantees of Full Recovery: This is the biggest tell. No one, not even the most skilled expert, can promise a 100% success rate. Blockchain recovery is a complex, uncertain process. Anyone offering a sure thing is selling snake oil.
- Demands for Upfront Fees: The classic advance-fee fraud. They'll ask for a "tax," "network fee," or "service payment" before anything happens. Once you pay, they'll vanish.
- Unsolicited Contact: Did a "recovery agent" conveniently slide into your DMs on Telegram, X, or Discord right after you posted about your loss? That's not a coincidence; it's a trap. Legitimate professionals don't hunt for clients in DMs.
- Requests for Your Seed Phrase or Private Keys: This should be an immediate dealbreaker. NEVER give your seed phrase or private keys to anyone, for any reason. If they ask, they're not trying to help you; they're trying to drain whatever you have left.
Your private keys are the absolute last line of defense for your remaining funds. Sharing them is like handing a thief the master key to your entire financial life. There is no legitimate scenario where a recovery specialist needs them.
The threat is very real. Highly organized groups, some linked to North Korea, were responsible for over $2.02 billion in losses in 2023 alone. These aren't small-time hackers; they are sophisticated operations targeting everyone from individuals to institutions. You can get more details on these large-scale crypto thefts to understand the professional nature of the threats we're all facing.
Legitimate Recovery Service vs Recovery Scam
Knowing who to trust is everything. Predatory scams and professional services might seem similar at first glance, but the differences become obvious when you know what to look for. It all comes down to their process, transparency, and what they ask of you.
This table breaks down the key differences to help you separate the pros from the predators.
| Characteristic | Legitimate Service | Typical Scam Tactic |
|---|---|---|
| Payment Model | Offers a free initial assessment; fees are often success-based or clearly outlined upfront. | Demands an upfront "fee" or "tax" with urgent pressure to pay immediately. |
| Communication | Uses official, secure channels like an encrypted website form or a professional business email. | Contacts you via unsolicited DMs on social media (Telegram, X, Discord). |
| Guarantees | Provides a realistic assessment of success chances, never promising a full recovery. | Guarantees 100% recovery to build false hope and lure you in. |
| Information Request | Asks for public information like transaction hashes and wallet addresses for analysis. | Asks for your seed phrase, private keys, or passwords to "sync" your wallet. |
A legitimate service works with you, using publicly available blockchain data. A scammer tries to get into your accounts.
Essential Privacy and Safety Practices
When you're reaching out for help, your own security has to be priority number one. The last thing you want is to create another vulnerability.
- Use Secure Communication Channels: Only engage with recovery services through their official website or verified business email. Never discuss sensitive details in public forums or social media DMs.
- Verify Their Credentials: Do your homework. Look for a professional website, case studies, and real-world reviews or testimonials. A legitimate business will have a verifiable track record.
- Set Up a New, Clean Wallet: If there's a chance of recovering any funds, you'll need a safe place to send them. Create a brand-new wallet that has never been connected to the compromised one.
Staying vigilant is your best defense. By recognizing these fraudulent patterns, you can avoid making a terrible situation even worse and focus on finding genuine, professional help that respects your security.
Common Questions About Crypto Recovery
When you're staring down the barrel of a crypto loss, your mind is probably racing with a million questions. It's a stressful, confusing time, and it’s easy to feel overwhelmed. Let's cut through the noise and get you some straight answers to the most common concerns.
Can Stolen Crypto Actually Be Recovered?
The honest answer? Sometimes. But it's never easy, and it really hinges on the specifics of your situation.
If your funds landed in an account on a major exchange like Coinbase or Binance, there's a sliver of hope. Act fast, and the exchange might be able to freeze the account. If the thief sent the funds to their own private wallet, however, it gets trickier. The trail is public on the blockchain, but actually getting the assets back usually requires the long arm of the law and some serious on-chain tracing.
And what if you just lost access? Maybe you forgot a password or a file got corrupted. In those cases, specialized recovery services can use some heavy-duty computational power to try and crack it. The key word there is try.
A word of warning: anyone who guarantees a 100% success rate is almost certainly running a scam. Real recovery work is complex and full of variables; there are no guarantees.
How Long Does This Process Take?
There’s no one-size-fits-all timeline. Getting your crypto back can be a waiting game, and how long you wait depends entirely on the problem.
Cracking a forgotten password on a wallet file could take a few days or a few weeks. It all comes down to the wallet's security and what clues you can provide. On the flip side, trying to claw back stolen funds through exchanges and law enforcement is a marathon, not a sprint. We're talking months, or in some tough cases, even years.
Your first moves—containing the damage and gathering evidence—need to happen in hours. The rest of the journey? That requires patience.
Will I Have to Pay a Fee for a Recovery Service?
Yes, but you should know exactly what you’re paying for. Legitimate recovery pros are upfront about their costs. They usually work on a success-fee basis, meaning they only get paid if you get your crypto back.
Huge red flag: any service demanding a big payment before they’ve even looked at your case. A reputable firm will always start with a confidential assessment to see if recovery is even plausible. Only after that will they talk numbers, which is typically a percentage of whatever they successfully recover for you.
What's the Single Most Important Step to Prevent This From Happening Again?
If you take away just one thing, let it be this: secure your seed phrase. Period. That string of 12 or 24 words is the master key to your entire crypto life.
Treat it like the deed to your house. Its protection is non-negotiable.
- Go analog. Write it down on paper or, even better, stamp it into metal. Never, ever take a picture of it or save it in a text file.
- Create backups. Keep copies in different, secure, physical locations. Think a safe at home and a safe deposit box at the bank. This protects you from fire, floods, or theft.
- Stay offline. Don't even think about saving it in the cloud, an email draft, or your password manager. The moment it touches an internet-connected device, it's vulnerable.
Pairing this with a hardware wallet is the best defense you can have. It keeps your private keys completely isolated from your computer, making it incredibly difficult for a hacker to get their hands on them.
If you're locked out of your wallet because of a forgotten password or a corrupted file, don't throw in the towel. Wallet Recovery AI uses advanced, secure methods to help you regain control of your assets. Request a confidential assessment today.


Leave a Reply