How to Store Cryptocurrency Safely: The Ultimate Real-World Security Guide
When you hear about safely storing cryptocurrency, it really boils down to one thing: taking full control of your private keys. The most reliable approach is a hybrid setup — a best-in-class hardware wallet for your long-term holdings, paired with a secure software wallet for smaller, everyday balances.
This strategy—known as self-custody—is the gold standard for cutting out third-party risk. It protects you from exchange hacks, frozen accounts, bankruptcies, and the silent killer of crypto portfolios: lost access.
The old saying in this space remains undefeated: Not your keys, not your crypto.
Reality check: Most crypto losses don’t come from breaking cryptography. They come from misplaced seed phrases, compromised backups, phishing attacks, and human error. This guide is built from real recovery cases—designed to give you a setup that’s secure, resilient, and recoverable.
Disclosure: The link above is an affiliate link and may earn a commission at no extra cost to you.
Why Your Crypto Storage Strategy Matters More Than Ever

Crypto offers financial sovereignty—but it also demands responsibility. Market volatility gets all the attention, but poor security wipes people out far more often. Leaving assets on an exchange is convenient, but it’s the digital equivalent of leaving cash on a park bench.
In a single year, over $4 billion in crypto was stolen—a nearly 40% increase year-over-year. The majority of losses weren’t smart-contract exploits; they were private key and seed phrase failures. Self-custody isn’t optional anymore—it’s survival.
The Core Principle of Self-Custody
Self-custody means you—and only you—control the private keys that move your funds. Exchanges introduce a single point of failure. When they fail, freeze withdrawals, or disappear, users learn the hard way that IOUs aren’t ownership.
Self-custody puts responsibility in your hands—but it’s the only way to eliminate third-party risk and achieve true financial sovereignty.
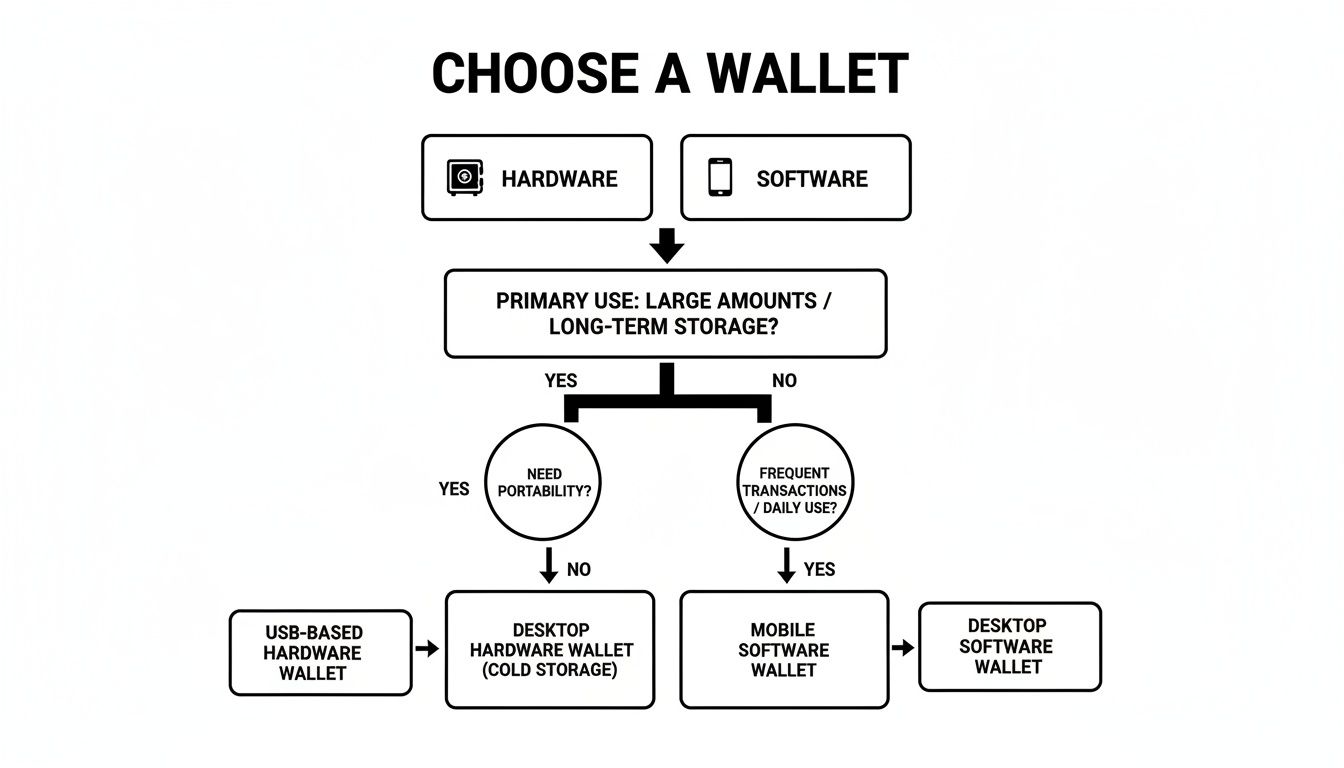
Choose Your Wallet: Hardware vs. Software
Your first major security decision is choosing the right wallet type. There are two categories that matter: hardware wallets (cold storage) and software wallets (hot storage). Each has a role—but confusing them is a costly mistake.
Why Hardware Wallets Are the Gold Standard
Hardware wallets keep private keys offline by design. Transactions are signed inside the device, never exposing keys to malware-infected computers or compromised browsers.
If you hold crypto you’d be devastated to lose, a hardware wallet isn’t optional—it’s mandatory.
Traditional options like Ledger and Trezor rely on a single recovery seed. More advanced designs, such as Cypherock X1, go further by removing the single-point-of-failure entirely through a split-key recovery model.
When Software Wallets Make Sense
Software wallets are ideal for DeFi, NFTs, and daily transactions—but they should only ever hold what you’re willing to lose. They’re connected to the internet, which makes them fundamentally more vulnerable.
Treat hot wallets like cash in your pocket. Cold wallets are your vault.
Mastering Your Seed Phrase: The Only Backup That Truly Matters
Your seed phrase is the master key to your entire crypto life. Lose it—and your funds are gone forever. Expose it—and your wallet can be drained in seconds.
Never Do These Things
- Never screenshot or photograph your seed phrase
- Never store it in cloud services or password managers
- Never email it or type it into a computer
Your seed phrase must never touch an internet-connected device. Ever.
Advanced Protection: The “25th Word”
Passphrases add a hidden layer of protection—even if someone finds your seed phrase, they still can’t access your real funds without the extra secret.
Advanced Strategies for Maximum Asset Protection

For large portfolios, single-wallet setups aren’t enough. Multi-signature wallets and air-gapped systems eliminate single points of failure and protect against both hackers and human mistakes.
Build Rock-Solid Daily Security Habits
Even the strongest hardware setup fails if daily habits are sloppy. Strong passwords, hardware-based 2FA, phishing awareness, and transaction verification are your first line of defense.
Most crypto losses are human failures—not technical ones.
Final Thought: Security That Survives Real Life
The best crypto storage strategy isn’t the most complex—it’s the one that survives real-world stress: device failure, human error, theft, and time. Hardware wallets form the foundation. Advanced designs like Cypherock X1 go further by eliminating seed-phrase single points of failure entirely.
If you’ve already lost access to a wallet due to forgotten passwords or damaged files, WalletRecovery.ai provides specialized, privacy-first recovery solutions. Learn how our AI-powered recovery service works.


Leave a Reply