That sinking feeling when you realize your Bitcoin is gone is gut-wrenching. It's a mix of panic, anger, and dread. But what you do in the next few minutes and hours can make all the difference between a total loss and a potential recovery.
Right now, clarity is your best weapon. Panic leads to mistakes. A calm, methodical approach is what’s needed to stop the bleeding, figure out what happened, and arm yourself with the evidence for the fight ahead.
Your Immediate Action Plan After a Bitcoin Theft
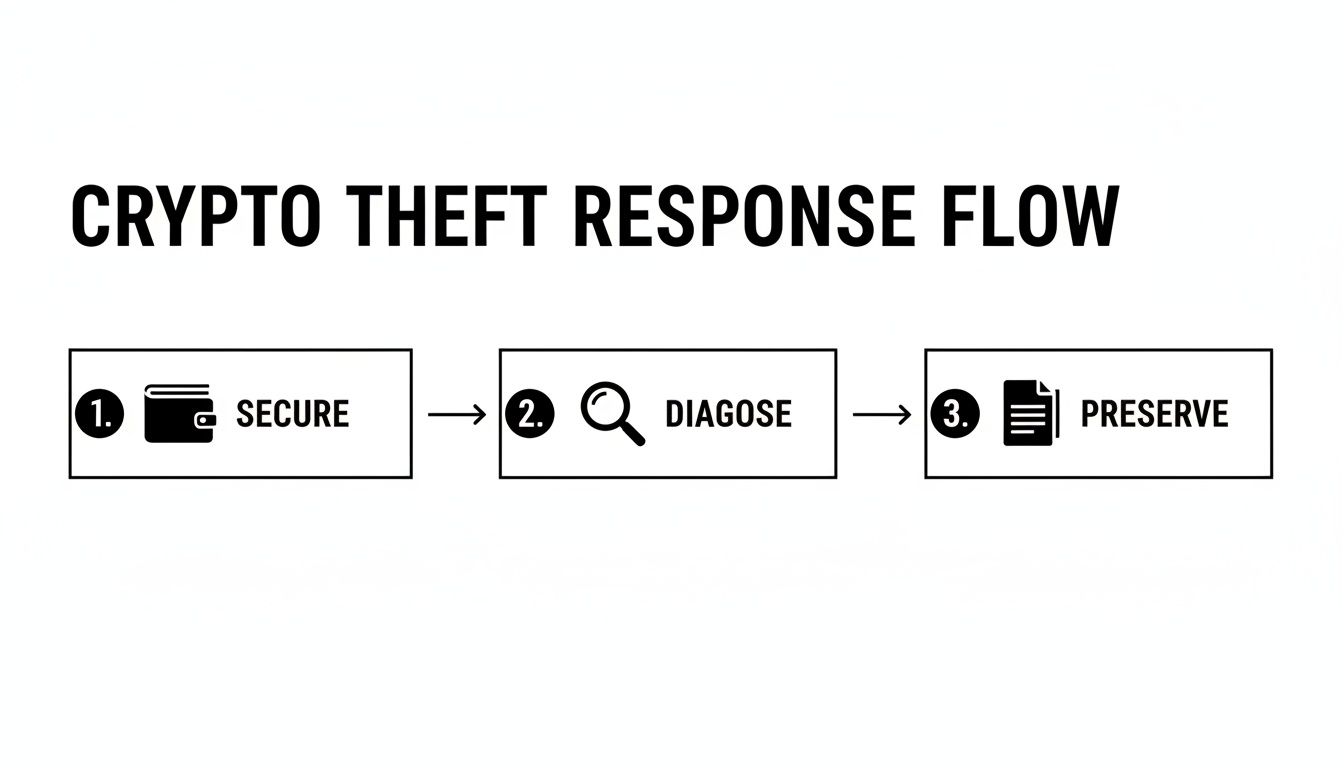
Think of this as digital triage. Your first priority is to contain the damage and preserve the crime scene. We'll walk through the three critical steps: securing what's left, diagnosing the breach, and gathering every shred of evidence.
This isn't just about damage control. You're laying the foundation for tracing your funds, dealing with exchanges, and potentially involving law enforcement.
Secure Any Remaining Assets First
Before you do anything else, protect what you still have. If the compromised wallet held other assets, or if you use the same credentials on other platforms, assume they're all at risk. The thief might still be in your system.
Your only move is to transfer every remaining fund to a brand-new, completely secure wallet. I can't stress this enough—it must be a wallet you've never used before, preferably set up on a different, clean device. This quarantines your remaining crypto and buys you time.
Diagnose the Attack Vector
With your other assets safe, it's time to put on your detective hat. How did they get in? Knowing the "how" is crucial for building a case and preventing it from happening again.
Run through these common scenarios:
- Phishing Scams: Did you click a link in an email or a direct message that looked legit but wasn't? These fake login pages are designed to harvest your private keys or seed phrase.
- Exchange Account Takeover: Check your account for weird login alerts, password changes, or newly generated API keys. Attackers often get in through weak passwords or a SIM-swap attack on your phone.
- Malware Infection: Your own computer could be the culprit. Keyloggers record everything you type, and clipboard hijackers are especially sneaky—they silently replace the wallet address you copy with the attacker's address just before you paste.
- Malicious Smart Contract: If you're active in DeFi, you might have accidentally approved a smart contract that gave a scammer permission to drain your wallet.
Understanding the point of entry is a huge piece of the puzzle for any recovery attempt.
Preserve Every Piece of Evidence
Now, start collecting everything. I mean everything. Don't delete a single email, message, or browser history entry, no matter how small it seems.
The digital breadcrumbs you gather right now are the most powerful tools you'll have. A single transaction ID, a screenshot of a fake website, or a chat log can be the one thing that helps an investigator trace your funds.
Start a dedicated folder and save it all. You'll need it for filing a police report, contacting an exchange's fraud team, or working with a recovery service.
Here's your checklist:
- Transaction IDs (Hashes): The unique identifiers for every fraudulent transaction.
- Attacker's Wallet Address: The address(es) your Bitcoin was sent to.
- Screenshots: Grab images of the phishing emails, malicious sites, chat messages, and transaction confirmations.
- Dates and Times: Note the exact time of the theft and any weird activity leading up to it.
- Communications: If you communicated with the scammer, save all of it—emails, Telegram chats, Discord messages, everything.
The first 24 hours are critical. To help you stay focused, here's a prioritized checklist of what to do right away.
Immediate Actions After Discovering Bitcoin Theft
| Priority | Action | Reasoning |
|---|---|---|
| Highest | Move all remaining funds to a new, secure wallet. | Prevents further losses. The attacker may still have access to the compromised wallet or device. |
| High | Disconnect the compromised device from the internet. | Stops any active malware from communicating with the attacker or spreading to other devices on your network. |
| High | Collect transaction IDs (hashes) and the attacker's wallet address. | This is the primary on-chain evidence needed to start tracing the stolen funds. |
| Medium | Screenshot all relevant evidence immediately. | Digital evidence can disappear. Capture phishing emails, websites, chat logs, and transaction details before they can be deleted. |
| Medium | Change passwords for all related accounts (email, exchanges). | Secures your digital identity and prevents the attacker from accessing other connected services. |
| Low | Run a full malware scan on all your devices. | Helps identify the potential attack vector (e.g., keylogger, remote access trojan) and cleans your system. |
Acting on these steps quickly and methodically provides the best possible foundation for any recovery effort that follows.
The reality of getting your crypto back can be tough. Crypto theft is a massive industry, hitting $3.4 billion recently, with sophisticated actors like state-sponsored groups from the DPRK becoming major players. While the odds can feel stacked against you, successful recoveries happen, and they almost always start with this kind of careful, immediate evidence preservation. You can find more insights into the challenges and successes of digital asset recovery at Deminor.com.
Following the Money: How to Trace Stolen Bitcoin on the Blockchain

When your Bitcoin gets stolen, it feels like it’s just gone—vanished into some digital black hole. But here’s the thing: it’s actually done the opposite. It has left a permanent, public trail on the blockchain.
This transparency is the single biggest tool you have in your investigation. The process is called on-chain analysis, and it's all about following the digital breadcrumbs the thief left behind. You won't see their name or face, but you can watch every single move their wallet makes. This data is pure gold when it's time to get exchanges or law enforcement involved.
Your First Stop: The Blockchain Explorer
The whole process starts with a blockchain explorer. Think of it as a search engine, like Google, but specifically for Bitcoin transactions. These are public websites that let anyone look up transactions, wallet addresses, and all sorts of on-chain data.
If you're new to this, we have a great guide that breaks down what a blockchain explorer is and how it all works.
To get started, you just need one of two things:
- The transaction ID (hash) of the theft itself.
- The thief's wallet address where they sent your funds.
Plug either one of those into an explorer, and you'll see a detailed record of the transaction—the exact amount, the sending and receiving addresses, and the timestamp. This is your first piece of the puzzle.
Playing Digital Detective
From this point on, your job is to become a digital stalker. You're going to watch that thief's address like a hawk. The second they move the funds, you follow them to the next address, and then the next one after that.
This is how you build a chain of evidence, documenting the entire journey of your stolen assets.
How Thieves Try to Cover Their Tracks
Criminals aren't stupid. They know you can follow them, so they rarely let stolen funds sit in a single wallet for long. Their main goal is to muddy the waters and make tracing as difficult as possible before they try to cash out.
A classic move is the peeling chain. A thief sends a small chunk of the stolen Bitcoin to one new wallet and the rest of the large balance to another. Then they repeat this, again and again, creating a messy web of transactions that "peels off" small amounts into dozens, sometimes hundreds, of different wallets.
Another favorite tactic is using a mixing service, often called a tumbler. These services throw funds from tons of different people and transactions into one big pot, shuffle them all up, and then send them out to new addresses. It's a deliberate attempt to break the on-chain link between the thief and the funds. It definitely makes tracing harder, but it's not a dead end for professional analysts.
The thief's endgame is almost always the same: move the funds to a centralized exchange to swap them for cash. This is their biggest weakness and your best shot at recovery. Exchanges with KYC (Know Your Customer) policies can freeze the account and will cooperate with law enforcement.
Documenting Every Step of the Way
As you trace the funds, you need to be meticulous. Every time the Bitcoin "hops" from one wallet to the next, you need to log the details. Fire up a spreadsheet and record the following for each move:
- Incoming Transaction ID: The hash of the transaction sending funds to the new wallet.
- Thief's New Wallet Address: The address that got the funds.
- Outgoing Transaction ID: The hash for when the thief moves the funds out again.
- Timestamp: The date and time for each transaction.
An organized log creates a clean, chronological map of the money trail. This isn't just for you; it's the hard, actionable evidence you'll give to exchange compliance teams and police. A vague report of theft is easy to brush off. A well-documented transaction trail is hard evidence that forces them to take action.
Alright, time to get the authorities and exchanges in the loop.
This part can feel like you're shouting into the void, but getting your reports filed correctly with exchanges and law enforcement is the only way you stand a chance of freezing the funds. Think of it this way: you’re laying the groundwork. Speed and precision are everything.
Scammers and thieves need a way to cash out. That "off-ramp" is almost always a major, centralized exchange. By sounding the alarm bells at these exchanges, you're essentially creating a digital roadblock. A well-documented, urgent report can hit an exchange's compliance desk and get the thief's account flagged before they can move the money into their bank account.
Getting the Exchanges on Your Side
Your mission here is to give the exchange's fraud team exactly what they need to act. A panicked, rambling email is going to get buried. A clear, evidence-based report gets escalated.
Treat it like you're submitting a professional incident report. It needs to be sharp and to the point.
- Make your subject line impossible to ignore. Something like:
URGENT: Stolen Funds Report – TX Hash [Paste the first few characters of the hash]gets straight to the point. - Give them your details. Full name and contact info, right at the top.
- Tell them what happened, fast. No long stories. "I was the victim of a phishing attack on [Date] at [Time], which led to an unauthorized transfer of my Bitcoin." That's it.
- Provide the on-chain proof. This is the make-or-break part. Give them the transaction hash(es) of the theft and the trail of wallet addresses you’ve already uncovered. This is the hard evidence their compliance team is looking for.
Now, a dose of reality. You're going to run into jurisdictional headaches. An exchange in Singapore might not be able to do much for a US citizen without a court order. But don't let that stop you. Most reputable exchanges will proactively freeze an account tied to credible theft reports while they wait for the official paperwork from law enforcement.
Bringing in Law Enforcement
Filing a police report does two things: it makes your claim official, and it's often the key that unlocks action from an exchange. Your local police department probably isn't staffed with on-chain sleuths, but that's not the point. You need to get an official report on file so it can be passed up the chain to cybercrime units.
When you file your report, give them the exact same evidence you sent to the exchanges. Make absolutely sure the transaction hashes and the thief's wallet addresses are written into the official report text. This creates the paper trail that connects your real-world identity to the on-chain crime.
If you're in the US, you have another critical step: file a report with the FBI's Internet Crime Complaint Center (IC3). This is the central hub for cybercrime in the country, and they're the ones who connect the dots between individual thefts to uncover larger criminal operations.
Here's what the IC3 homepage looks like. This is where you'll start your report.
Getting your case into their national database is a huge step. It drastically increases the odds that your theft will be linked to others, painting a much bigger picture for investigators.
Pro Tip: Your police report number is gold. Once you have it, go back to every exchange you contacted and update your ticket. Referencing an official case number gives your claim immense credibility and often fast-tracks it through their internal process.
It’s important to keep your expectations in check here. Law enforcement is swamped, and international crypto cases are a nightmare to investigate. You won't get an instant fix. The goal of this step is to build the official foundation that empowers exchanges, lawyers, and recovery specialists to do their jobs. Your persistence in delivering clean, organized evidence is what will make your case stand out.
So, you’ve traced the transaction, filed the reports, and now… you’ve hit a brick wall.
The digital trail has gone cold. Exchanges are giving you the runaround. The sheer technical mess of it all feels like a mountain you can’t climb. This is the moment for a gut check. Is continuing on your own the best move, or is it time to bring in a specialist?
Deciding to hire a professional to recover stolen crypto is a big step, and choosing the right one is absolutely critical to avoid making a bad situation even worse.
First, you need to understand the landscape. Not all "recovery" services are created equal. The industry really breaks down into two main camps.
On one side, you have asset recovery firms. Think of them as the legal eagles. These teams are typically made up of lawyers, forensic accountants, and private investigators who live and breathe the legal system. They're your best bet for large, complex cases that are going to require court orders, international legal battles, and forcing regulated companies to cooperate.
On the other side are technical recovery specialists. These are the code crackers and digital locksmiths. They don't focus on theft, but on access. Their expertise is in brute-forcing lost passwords, rebuilding corrupted wallet files, or pulling assets off damaged hardware wallets. They use powerful computational tools to get back into wallets you own but are locked out of.
Red Flags: The Hallmarks of a Recovery Scam
Before you even think about hiring anyone, you have to learn how to spot the sharks. The crypto world is swimming with fake "recovery agents" who prey on the desperation of victims. They promise you everything and deliver nothing, leaving you with even less than you started with.
Be incredibly skeptical of any service that guarantees they'll get your money back. The hard truth is that crypto recovery is insanely difficult. No legitimate professional will ever offer a 100% guarantee. This is the single biggest red flag.
Keep an eye out for these classic scam tactics:
- Upfront Fees: Reputable services almost always work on a contingency fee—they take a percentage of the funds after they're recovered. Anyone asking for a big payment upfront to "start the process" or "unlock the blockchain" is almost certainly a scammer.
- Asking for Your Seed Phrase or Private Keys: Never. Ever. Share this information. A real recovery service will never need your private keys. Giving them up is like handing a thief the master key to your entire financial life.
- Vague Methods: If they can’t explain their process clearly, run. Phrases like "hacking back the funds" or using "secret blockchain exploits" are pure fantasy and massive red flags.
Vetting a Legitimate Service
Finding a partner you can trust comes down to good old-fashioned due diligence. A legitimate firm will be transparent about its methods, fees, and past results.
Start by looking for a real-world presence. Do they have a professional website? Case studies? Verifiable testimonials? A trustworthy service will have a clear digital footprint that goes beyond a few random social media profiles. Before you decide, it’s worth understanding what a credible assets recovery company looks like so you know what to look for.
When you make contact, come armed with questions:
- What’s your fee structure? Get it in writing. It should be a straightforward percentage of recovered assets, with zero hidden charges.
- What is your exact process? They should be able to walk you through their on-chain analysis, legal strategy, or technical recovery methods without hiding behind jargon.
- Can you provide references or case studies? While client confidentiality is key, they should be able to offer anonymized success stories or point you toward public records of their work.
- What information do you need from me? Their requests should be limited to transaction IDs, wallet addresses, and evidence—never your private keys or login credentials.
It's easy to focus on theft, but a staggering amount of crypto is simply lost, not stolen. A 2023 report estimated that up to 3.8 million Bitcoins are considered lost forever.
However, experts believe a small but mighty chunk of that—potentially worth as much as $11 billion—could be salvaged with the right technical skills. You can learn more about the findings on recoverable crypto assets in Bankrate's detailed analysis. This is precisely where technical specialists shine, using their expertise to unlock wallets that owners thought were gone for good.
DIY Recovery vs. Professional Services
Making the call between going it alone and hiring help can be tough. The right choice depends on your specific situation, technical skills, and the complexity of your case. This table breaks down the key differences to help you decide.
| Aspect | DIY Approach (Do-It-Yourself) | Professional Service (e.g., Wallet Recovery AI) |
|---|---|---|
| Cost | Free (besides your time and any software tools) | Typically a percentage of recovered funds (contingency fee) |
| Expertise Required | High. Requires deep knowledge of blockchain analysis, forensics, and legal procedures. | None. You rely on the firm's specialized skills and experience. |
| Tools & Technology | Limited to publicly available or consumer-grade software. | Access to advanced proprietary software, powerful hardware, and investigative databases. |
| Time Commitment | Extremely high. Can consume weeks or months of full-time effort. | Minimal. You provide initial information; they handle the legwork. |
| Success Rate | Low, especially in complex theft cases or for difficult technical recoveries. | Significantly higher due to expertise, resources, and established processes. |
| Risk | High risk of making mistakes, hitting dead ends, or falling for secondary scams. | Low risk. Reputable firms operate under clear agreements and have a track record. |
Ultimately, a DIY approach is best suited for straightforward cases where you have a strong technical background and a lot of time. For anything else—especially high-value losses or complex technical challenges—bringing in a professional service dramatically increases your odds of a successful recovery.
Strengthening Your Crypto Security for the Future
After the frantic, gut-wrenching process of trying to recover stolen funds, the dust eventually settles. But it leaves behind a critical question: what now? The only way forward is to turn this painful experience into a powerful lesson, hardening your defenses to make damn sure it never happens again.
This isn't about rehashing the same old advice you've heard a dozen times. "Use a strong password" isn't going to cut it. This is a strategic overhaul of your security, adopting the same high-impact measures that seasoned crypto veterans live by. It’s about building layers of protection that make you a much, much harder target for thieves.
Embrace Hardware Wallets for True Cold Storage
The single most effective change you can make, starting today, is to move your assets into a hardware wallet.
Software wallets, whether on your computer or phone, keep your private keys on an internet-connected device. That’s a huge vulnerability. Hardware wallets, on the other hand, keep your keys completely offline in a secure chip. This is what we call "cold storage."
Think of it like this: a software wallet is like keeping cash in your pocket—convenient, but easily snatched. A hardware wallet is your own personal bank vault. Even if your computer is riddled with malware, a thief can't get to your keys because they never touch the internet. The device signs transactions offline and only broadcasts the approved signature back to the network.
For anyone serious about protecting their crypto, this is non-negotiable. Industry leaders like Ledger and Trezor make robust devices that create a physical barrier between your most critical data and online threats.

This physical separation is the whole point. It's the core principle that makes hardware wallets so incredibly resilient against the most common types of crypto theft.
Distribute Risk with Multi-Signature Wallets
If you're managing significant holdings, it's time to level up to a multi-signature (multisig) wallet. While a standard wallet needs just one key to approve a transaction, a multisig setup requires multiple keys to sign off.
A common setup is a "2-of-3" wallet. This configuration generates three separate private keys, but you only need any two of them to move funds. You can then store these keys in completely different physical locations.
- Key 1: Stored on your primary hardware wallet.
- Key 2: Kept with a trusted family member or in a bank's safe deposit box.
- Key 3: On a backup hardware wallet, stored in another secure spot.
This setup creates incredible resilience. A thief could steal one of your keys, and they still couldn't touch your crypto. If you accidentally lose one, you can still recover everything with the other two. It completely eliminates single points of failure.
A multi-signature wallet changes the security game from protecting a single secret to protecting a distributed system. It's one of the most powerful tools available for safeguarding substantial crypto wealth against both theft and accidental loss.
Master Your Operational Security Habits
Beyond the tech, your daily habits—what we call operational security (OpSec)—are just as important. Thieves don't just exploit code; they exploit human behavior.
Start by locking down these essential OpSec practices:
- Use a Dedicated Device: If you can, get a specific laptop or tablet that you only use for crypto transactions. No casual browsing, no personal email, no downloading random files. This drastically shrinks your exposure to malware.
- Become a Phishing Skeptic: Scrutinize every email, DM, and link. Before connecting your wallet, double- and triple-check that the website's URL is legit. A common trick is using a domain that looks almost right (e.g., "coinnbase" instead of "coinbase").
- Avoid Public Wi-Fi for Transactions: Never, ever manage your crypto on a public network at a café, airport, or hotel. These networks are often unsecured, making it child's play for an attacker to intercept your data.
- Rethink Your Seed Phrase Backup: Do not store your seed phrase digitally. That means no photos, no cloud drives, and no password managers. Write it down on paper, or better yet, stamp it into metal plates to make it fireproof and waterproof. Store these physical backups in separate, secure locations.
Strengthening your security isn’t a one-and-done task; it’s an ongoing commitment. By combining the physical security of hardware wallets, the distributed trust of multisig, and the disciplined habits of strong OpSec, you build a layered defense that makes a repeat theft exceptionally unlikely. This is the mindset that ensures your long-term safety in the crypto world.
Your Top Questions About Stolen Bitcoin Recovery, Answered
When you've been a victim of crypto theft, your head is spinning with questions. It's a confusing and stressful time. Let's cut through the noise and tackle the most common things people ask, giving you the direct, no-nonsense answers you need to figure out what comes next.
Is Recovering Stolen Bitcoin Actually Possible?
It's tough, but it's not a lost cause. The real question is where the thief sent your funds. If they moved your Bitcoin into an account at a major, regulated exchange—one that requires customer identification (KYC)—then you have a fighting chance. Getting those assets frozen and returned requires a quick, coordinated effort between you, the exchange's compliance team, and law enforcement.
The game gets much harder, though, if the thief knows what they're doing. If they use tools like coin mixers to obscure the trail or move the funds into the decentralized finance (DeFi) world, tracing and recovery become exponentially more difficult. Your biggest weapon here is speed. The faster you can trace the funds and get the word out to exchanges, the better your odds.
What Does a Crypto Recovery Service Usually Cost?
This is where you need to be incredibly careful. Any legitimate, reputable recovery firm will almost always work on a contingency fee. That means you pay them nothing upfront. Their fee is a percentage of the funds they successfully get back for you.
You can expect this success-based fee to be anywhere from 10% to 40%. The exact number depends on how complex the case is, how much was stolen, and the technical work involved.
Be on high alert for anyone demanding a big payment before they start. Phrases like "investigation fee" or "unlocking charge" are giant red flags. This is the classic signature of a recovery scam, designed to bleed you for even more money. Always, always get the fee structure in writing before you agree to anything.
The Scammer Asked For More Money to Get My Bitcoin Back. Should I Pay?
No. Absolutely not. This is a cruel but predictable trick right out of the scammer's playbook. After the initial theft, they’ll often re-engage with a new story, claiming you need to pay a "tax" or a "transaction fee" to release your original funds.
It’s a lie. Every single time. Sending them more money only guarantees you lose more money. They will keep inventing new reasons for you to pay for as long as you're willing to send it. Your only move here is to cut off all communication immediately. The only thing you should do is document the new wallet addresses they provide and add them to your law enforcement report.
How Long Does This Whole Recovery Process Take?
There’s no easy answer here—the timeline is all over the map. It could be a few weeks, or it could be several years.
- Best-Case Scenarios: If you act fast and the funds are frozen quickly on a centralized exchange, you might see a resolution in a matter of weeks or months.
- The Long Haul: Cases that require legal orders, international law enforcement cooperation, or a deep, complex investigation can drag on for a very long time, with no guarantee of a positive outcome.
You have to be prepared for a marathon, not a sprint. Patience and realistic expectations are your best friends here. Recovering stolen Bitcoin is a slow, methodical process that requires persistence.
If your crypto is locked away because of a lost password or a technical glitch, Wallet Recovery AI can help you regain access securely and privately. Our AI-powered approach offers a proven way to restore control over your digital assets. Find out more at https://walletrecovery.ai.


Leave a Reply