Think of your Bitcoin wallet's private key as the literal key to your digital treasure chest. So, what is bitcoin wallet encryption? It’s the process of forging a high-tech lock for that chest, a lock that only a specific password—your password—can open. It essentially scrambles your private keys, turning them into unreadable gibberish for anyone who doesn't have the secret passphrase.
What Bitcoin Wallet Encryption Means for Your Security

An unencrypted wallet is like leaving a stack of cash on your kitchen table. If someone breaks into your house, that cash is gone. Encryption is the equivalent of taking that cash, locking it in a vault, and creating a combination that only you know. It's the first and most critical line of defense if your computer, phone, or even a backup drive falls into the wrong hands.
Without it, a thief who gets access to your device could simply copy your wallet file and drain your funds. This is why bitcoin wallet encryption isn't just a nerdy feature—it's the bedrock of securing your assets against straightforward theft.
The Role of Your Password
Here's the catch: your wallet's security is only as strong as the password you use. A weak password like "password123" is like putting a flimsy screen door on a bank vault. Hackers use sophisticated software that can blast through millions of combinations per second, making those simple passwords completely useless.
On the other hand, a strong, unique password creates a nearly unbreakable barrier. The math behind the encryption algorithms is so powerful that even a supercomputer would take an impossibly long time to guess the right combination.
It boils down to a simple partnership:
- Encryption is what scrambles your private keys into nonsense.
- Your Password is the only thing that can unscramble them back into something useful.
Malware designed specifically to hunt for cryptocurrency wallet files is a constant threat. For example, threats like StilachiRAT actively scan infected computers for wallet data, which is exactly why encryption is a non-negotiable security layer.
Why Encryption Is a Double-Edged Sword
While it’s your best defense, encryption introduces a brand new risk: you. You become the single point of failure. If you forget your password, the same powerful fortress that locks thieves out also locks you out. There’s no "forgot password" button to click. Your funds become prisoners, trapped behind the very wall you built to protect them.
This is the fundamental trade-off of self-custody. You get total control over your money, but that comes with total responsibility for securing—and remembering—how to access it.
Because of this, truly mastering bitcoin wallet encryption means developing two separate skills:
- Creating a password tough enough to stop an attacker cold.
- Building a bulletproof system to make sure you never, ever lose that password.
Ultimately, encryption is the tool that lets you be your own bank. Understanding how it works is the first step toward managing your crypto with confidence, knowing your funds are safe from both hackers and your own future forgetfulness.
Here are the most common encryption formats you’ll run into.
Think of bitcoin wallet encryption like different models of digital safes. They all exist to protect your private keys, but each has its own design, purpose, and rules for getting inside. Knowing which kind of digital vault you're working with is the first critical step for both security and, if things go wrong, recovery.
These formats aren't just technical jargon; they are the very containers holding the keys to your crypto. You wouldn't store gold bars in a shoebox, and you shouldn't use the wrong encryption format for the job. Let's break down the main types.
The Classic Vault: Wallet.dat
If you’ve ever run the original Bitcoin Core client, the wallet.dat file is an old friend. Imagine it as a master vault that doesn't just hold one key, but your entire keychain. It bundles a whole collection of your private keys, public keys, and transaction history into a single file.
When you set a password on your Bitcoin Core wallet, what you're actually doing is encrypting this entire wallet.dat file.
- What it does: It’s a complete database for every key and transaction tied to a Bitcoin Core wallet.
- How it’s secured: Once encrypted, the file is gibberish without the right password. If an attacker steals the file, they can't get to the keys inside unless they can also crack your password.
- The risk: Because it holds everything, losing the password to an encrypted
wallet.datlocks you out of all your funds at once. File corruption is another real danger that could make the entire key collection useless.
This all-in-one design was the standard for early Bitcoin adopters, but its monolithic nature also means it's a single point of failure if you're not careful.
The Single-Key Safe: BIP38 Encryption
In sharp contrast to the multi-key wallet.dat vault, BIP38 encryption is more like a small, ultra-secure case built to protect just one private key. It’s a standard way to encrypt a single key with a passphrase, which transforms it into a new, password-protected string of characters.
This format is fantastic for creating paper wallets or for securely moving a single private key from one place to another. You can print a BIP38 encrypted key and leave it on your desk, knowing that even if someone finds it, they still need the password to do anything with it.
Key Takeaway: BIP38 effectively turns a private key into a two-factor asset: something you have (the encrypted key) and something you know (the password). You need both to spend the bitcoin, which dramatically improves security for offline storage.
Modern Standards: Seed Phrases and Keystore Files
As crypto matured, so did the methods for securing keys. Most modern wallets have shifted to more flexible and user-friendly systems built around mnemonic seed phrases and structured data files.
Encrypted Seed Phrases (BIP39 Passphrase)
The vast majority of today's wallets use a BIP39 seed phrase—that familiar list of 12 to 24 words—as the ultimate backup for all your private keys. For an extra layer of security, BIP39 includes an optional passphrase, often called the "25th word." This isn't a password that encrypts the seed words themselves. Instead, it works with the seed to generate a completely new and separate wallet.
- Your 24-word seed phrase generates Wallet A.
- Your 24-word seed phrase + the passphrase "apple" generates a totally different Wallet B.
- Your 24-word seed phrase + the passphrase "Apple" generates yet another Wallet C (yes, passphrases are case-sensitive).
This creates what’s called plausible deniability. Even if someone forces you to give up your 24-word seed phrase, they'll only see Wallet A; they won't even know that your real funds are hidden in Wallet B, protected by your secret passphrase.
Keystore JSON Files
You'll see keystore JSON files everywhere in the Ethereum world, but they're used for other cryptos, too. A keystore file is simply a structured text file (using the JSON format) that contains a single encrypted private key. It also handily includes metadata about the encryption itself, like the specific algorithms used.
This self-contained format is great because it bundles the key and its security settings together. To get to the funds, you need both the keystore file and the password used to create it. It strikes a nice balance between portability and security, which is why it's a popular choice for many web and software wallets.
How Encryption Algorithms Protect Your Wallet
If your password is the key to your digital vault, then encryption algorithms are the powerful engines that forge that key into something impossibly complex. These engines are called Key Derivation Functions, or KDFs. Their entire job is to take a simple, human-memorable password and transform it into a long, random, and incredibly strong cryptographic key.
This transformation isn't a simple one-to-one swap. A KDF intentionally makes the process slow and difficult. Think of it like a master blacksmith forging a sword: it involves heating, hammering, and folding the metal over and over again. This deliberate, resource-intensive process is what gives your bitcoin wallet encryption its muscle.
The whole point is to make it astronomically expensive for an attacker to guess your password. Even if they get their hands on your encrypted wallet file, a strong KDF ensures that trying to brute-force their way in would require an absurd amount of time and computing power.
Salting and Stretching: Your Password's Bodyguards
To get to that level of security, KDFs use two critical techniques: salting and stretching. They work as a team to turn even a decent password into a formidable defense.
Salting is like adding a unique, secret ingredient to your password before it gets mixed. A "salt" is just a random piece of data that's combined with your password. This means even if two people use the exact same password—say, "Satoshi123"—the final encryption key will be completely different for each because their salts are unique. This completely shuts down attackers who use pre-computed tables of common password hashes, known as rainbow tables.
Stretching, on the other hand, is the process of running the encryption function thousands, or even millions, of times. Each repetition, or "iteration," makes the process of checking a single password guess slower. This is where the blacksmith analogy really hits home—every iteration is another fold and hammer strike, making the final key stronger and way harder to reverse-engineer.
- Salting: Adds uniqueness to stop mass attacks in their tracks.
- Stretching: Adds computational work to slow down every single guess.
Together, these techniques send the cost of an attack through the roof. An attacker can't just test billions of passwords a second; they're forced to do the same slow, heavy lifting for every single guess that your computer did just once when you set the password.
Comparing the KDF Powerhouses
Not all KDFs are built the same. As attackers have gotten access to more powerful hardware over the years, new algorithms have been developed to stay ahead. Here are the three main players you'll run into in the world of bitcoin wallet encryption.
This diagram shows how different encryption formats act as containers for your keys.
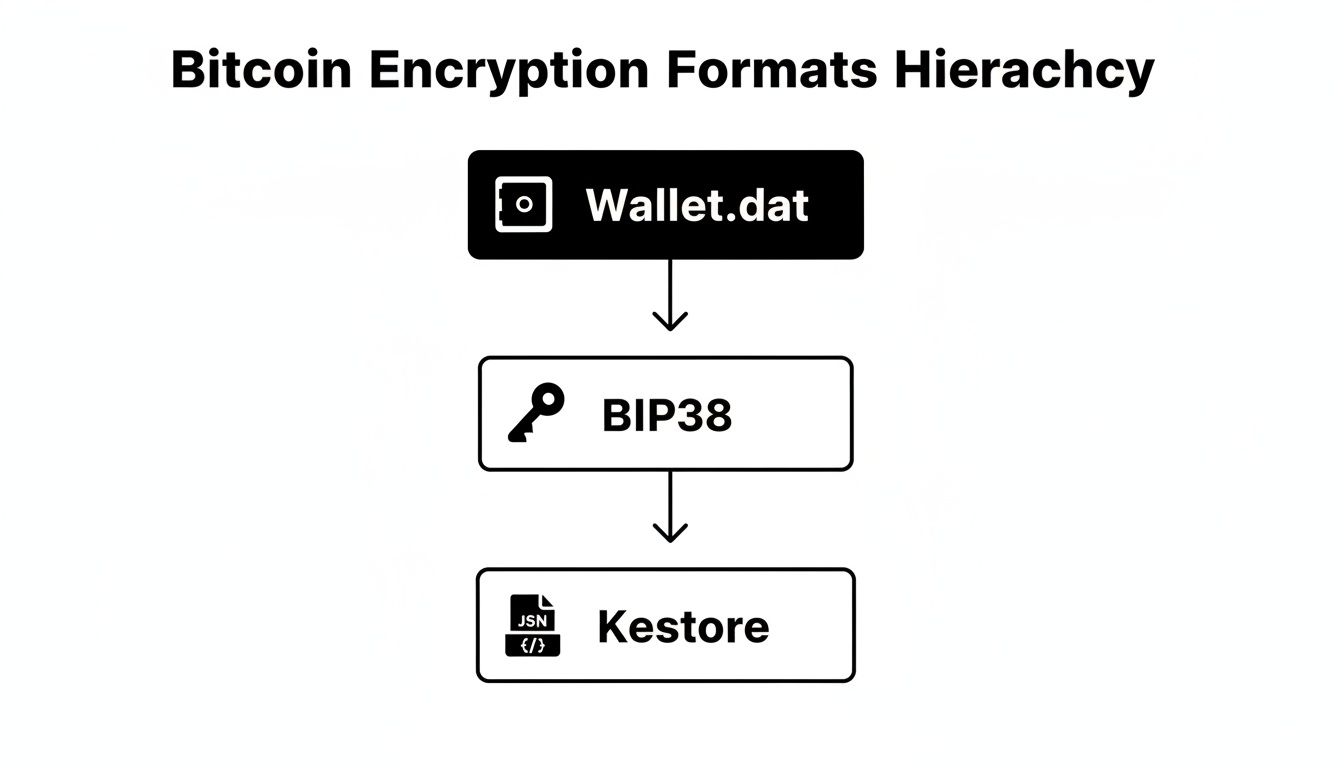
Each of these formats, from the big Wallet.dat vault to the single-key BIP38 and modern Keystore files, relies on these underlying KDFs to keep things locked down.
PBKDF2 (Password-Based Key Derivation Function 2)
PBKDF2 is the old guard of KDFs. It's been around the block, is incredibly well-tested, and relies purely on stretching (computational intensity) to slow down attackers. It basically forces a hacker's computer (CPU) to grind away for every guess. While it's still secure when set up with a high number of iterations, its biggest weakness is that powerful, specialized hardware like GPUs can speed up the process by running many guesses in parallel.
scrypt
Developed specifically to fight the GPU threat that PBKDF2 faces, scrypt is not only computationally intensive but also memory-intensive. It requires a hefty amount of RAM to run, something a normal computer has plenty of but is very expensive to build into the specialized chips (ASICs) that attackers use for brute-forcing. This "memory-hard" design gives it a huge advantage over PBKDF2.
By forcing attackers to use a ton of memory for each guess, scrypt levels the playing field. It makes it far more expensive for them to build specialized password-cracking machines.
Argon2
Argon2 is the modern champion, having won the official Password Hashing Competition back in 2015. It was designed to be the best of all worlds. It’s not only CPU-hard and memory-hard but also highly resistant to being parallelized. It comes in several flavors, including Argon2id, which combines resistance to both timing attacks and GPU-based cracking.
It's also highly tunable, letting developers perfectly balance memory usage, computation time, and parallelism to create the strongest possible defense. For this reason, Argon2 is now considered the gold standard and is what we recommend for any new application needing rock-solid bitcoin wallet encryption.
Here's a quick look at how these three KDFs stack up against each other. Each was designed to solve a specific problem, and their evolution tells the story of the cat-and-mouse game between security experts and attackers.
Comparing Common Key Derivation Functions (KDFs)
| KDF Name | Primary Feature | Resistance To | Commonly Used In |
|---|---|---|---|
| PBKDF2 | Computationally intensive (stretching) | CPU-based attacks | Older wallet formats, Wi-Fi (WPA2) |
| scrypt | Memory-intensive ("memory-hard") | GPU and ASIC-based attacks | Litecoin, many altcoins, some password managers |
| Argon2 | Balanced memory and computation, tunable | GPU, ASIC, and side-channel attacks | Modern applications, Ethereum keystores |
Ultimately, while the underlying technology is complex, the goal is simple: make it so tough for an attacker to guess your password that they don't even bother trying. Choosing wallets that use modern KDFs like Argon2 or a well-configured scrypt is a huge step in the right direction.
Common Failure Modes and Wallet Access Issues

While bitcoin wallet encryption is a powerful shield against thieves, it can quickly turn into an impenetrable wall locking you out of your own assets. It's a double-edged sword, and it's the reason behind countless stories of lost crypto. The very security measures designed to protect you become the barrier.
Understanding these common points of failure is the first step toward avoiding a digital disaster.
The most frequent issue is painfully simple: a forgotten password. Unlike your bank, there's no customer service line to call for a reset. Your memory is the only key. When it fails, the encryption does its job perfectly—it keeps everyone out, including you.
Even a single typo can be catastrophic. A misplaced capital letter, a forgotten symbol, or a simple fat-finger mistake is all it takes to lock yourself out for good.
Beyond Forgotten Passwords
Memory lapses are the biggest culprit, but they're far from the only threat. The very files that hold your encrypted keys can also become a critical point of failure, turning a simple software glitch into a financial catastrophe.
-
File Corruption: Your
wallet.dator keystore JSON file can get corrupted from a hard drive failure, an improper shutdown, or a software bug. When that happens, even the right password won't work because the data it's supposed to unlock is scrambled and unreadable. -
Incomplete Backups: Many people are diligent about backing up their wallet files but forget to save all the necessary pieces. Forgetting to include the latest keypool data or backing up an outdated
wallet.datfile can mean any funds received after the backup are completely inaccessible. -
Hardware Failure: Storing your only encrypted wallet file on a single laptop or USB drive is a high-stakes gamble. If that device is lost, stolen, or damaged beyond repair, your encrypted data—and the bitcoin it secures—is gone with it.
A strong password and flawless encryption are only as good as the file they protect. If the digital container holding your keys is corrupted or lost, the password becomes a key to a door that no longer exists.
Subtle Bugs and Flawed Implementations
Sometimes, the failure isn't your fault at all. The problem can be hidden deep within the wallet software itself. These subtle issues can undermine your security no matter how strong your password is. A bug in the key generation process or a weak implementation of an encryption standard can create a fatal flaw.
For example, even with a strong password, if the wallet software generates private keys with poor randomness, the bitcoin wallet encryption is just a facade. Researchers once disclosed a major vulnerability in a widely used library that exposed over 120,000 private keys due to a flawed random number generator. This proves that encryption alone isn't enough; the entire security chain has to be solid.
This reality underscores a critical point: you are trusting the software's developers to have implemented everything perfectly. When they don't, your funds are at risk.
Forgetting a password is one of the most common reasons users need help, but there are structured ways to approach the problem. If you find yourself locked out, our guide on how to recover forgotten passwords provides essential strategies and next steps. Recognizing these failure modes shows why, in many complex cases, DIY recovery attempts can be risky and why professional assistance is often the safest and most effective path forward.
The High Cost of Weak or Forgotten Encryption
To really get why strong bitcoin wallet encryption is a must-have today, you just have to look back at Bitcoin's wild west beginnings. In the early days, security was often an afterthought. Wallet encryption was optional, weak, and most people didn't really understand it, which led to a digital graveyard of lost coins.
This wasn't some small hiccup; it changed the entire Bitcoin landscape forever. A huge chunk of the total supply was lost, not to sophisticated hackers, but to simple things like forgotten passwords, corrupted files, and user error. This history is a stark reminder of the massive financial price of weak security.
A Fortune Lost to Time
The sheer scale of this loss is hard to wrap your head around. The casual attitude toward security in Bitcoin's infancy directly created a massive pool of permanently inaccessible coins. A 2020 study estimated that around 3.7 million Bitcoin—that's roughly 20% of all Bitcoin that will ever exist—might be gone for good. At an average price of $60,000, we're talking about over $220 billion locked away in digital time capsules.
That staggering number really puts the consequences of failed access into perspective. The problem itself isn't new, but as Bitcoin's value has gone through the roof, the stakes have become astronomically higher.
The lesson from Bitcoin's early years is crystal clear: the biggest threat to your crypto isn't always an outside attacker. More often than not, it’s a failure in your own security and recovery plan that poses the greatest risk.
The Evolution of Risk and Recovery
While the problem of lost access has always been there, the specifics have changed. Early losses were often due to basic mistakes, like not encrypting a wallet at all or simply losing a hard drive. Today, the challenges are a bit more complex, usually involving forgotten passphrases for highly secure encryption or dealing with corrupted wallet files that need an expert touch.
This history lesson hammers home just how important it is to be diligent with your security. It’s not enough to just encrypt your wallet; you also need a rock-solid plan for keeping your credentials safe. Understanding the importance of a good bitcoin wallet backup strategy is every bit as critical as picking a strong password.
In the end, the ghost wallets of Bitcoin’s past are a constant warning. The high cost of forgotten encryption is measured in billions, proving that strong security and a reliable recovery plan are two sides of the same essential coin.
When to Seek Professional Wallet Recovery

The crypto world is built on a "do it yourself" ethos, but sometimes, trying to recover a locked wallet on your own can do more harm than good. It's a tough pill to swallow, but pushing ahead with the wrong tools or a shaky understanding of the tech can turn a recoverable problem into a permanent loss.
Knowing when to call in an expert isn't giving up; it's a smart move to protect your assets. The landscape of bitcoin wallet encryption is littered with technical landmines, and one wrong step can be devastating.
Triggers That Signal You Need an Expert
If you're nodding along to any of the scenarios below, it's a huge red flag. Going it alone from here dramatically increases the risk of making a fatal error, like accidentally overwriting the very data you’re trying to save.
-
Suspected File Corruption: Your
wallet.dator keystore JSON file just won't load. It feels corrupted. Firing up random repair tools you found online is a great way to scramble that data forever. Professionals use specialized forensic software to carefully analyze and repair file structures without touching the original. -
Unusual or Obscure Encryption: Are you wrestling with a wallet from some long-dead, forgotten crypto project? These often used funky, non-standard encryption methods that modern recovery tools simply don't understand.
-
Hardware Failure: A clicking hard drive, a dead SSD, or a physically snapped USB stick is not a DIY job. These situations require a cleanroom environment and forensic hardware to safely pull the wallet data off the platters or chips. Any attempt to "fix" it yourself will almost certainly destroy the drive—and your crypto along with it.
-
Complex Password Scenarios: You kind of remember the password… but was it "correct horse battery staple" or "CorrectHorse-Battery-Staple123"? When you have dozens of possible variations, trying to brute-force it on your home computer is like trying to empty the ocean with a teaspoon. Pro services use massive computing clusters to test trillions of combinations systematically and efficiently.
How to Engage a Recovery Service Securely
Handing over anything related to your wallet to a third party sounds terrifying, and it should. But reputable services are built on one core principle: non-custodial recovery. This is non-negotiable. It means you should never, ever hand over your unencrypted private keys or your seed phrase.
A trustworthy recovery service helps you find the key to your own lock; they don't ask for a copy of it. Their entire process is designed to help you regain access, making sure you're the only one who ever touches the funds.
The whole process should feel transparent and secure. A legitimate service, for example, might give you a piece of software to run on your own computer. This tool can communicate with their powerful servers to test password candidates without your actual wallet file ever leaving your machine.
Services like Wallet Recovery AI are built around this secure, privacy-first approach.
This model ensures your wallet file and potential private keys stay firmly in your possession, securing the entire recovery attempt. By sticking to a non-custodial model, you can get the expert help you need without ever losing control of your assets.
A Few Common Questions About Wallet Encryption
When you're dealing with something as important as securing your bitcoin, questions are bound to pop up. It's totally normal. Is the encryption really strong enough? What's the deal with passwords versus seed phrases? Let's clear up some of the most common points of confusion.
Think of this as a quick-and-dirty FAQ to help you wrap your head around wallet security and what it means for getting your funds back if something goes wrong.
Can Bitcoin Wallet Encryption Actually Be Broken?
Short answer? No, not really. At least, not by brute force with any technology that exists today. When it's done right, modern wallet encryption is a digital fortress. Trying to crack a strong, complex password would take even the most powerful supercomputers thousands, if not millions, of years.
But there's a catch—the strength of that fortress depends entirely on the password you choose. The encryption itself isn't the weak link; we are. A simple or predictable password can be guessed in a shockingly short amount of time with the right hardware.
This is a key point: a professional recovery service doesn't "break" the encryption. What we do is run a methodical, high-speed search for your forgotten password. We're testing millions of your own likely variations to find the one that unlocks the wallet, just like you would if you had enough time and computing power.
What’s the Difference Between a Wallet Password and a Seed Phrase?
It's super easy to mix these two up, but they have completely different jobs.
- Your Seed Phrase is the master key to everything. It's that list of 12 or 24 words that can rebuild your entire wallet from scratch on any new device. Lose this, and you've lost it all.
- Your Wallet Password is more like a lock on the front door of your house. It just encrypts the local wallet file on your computer or phone, stopping anyone who gets their hands on your device from opening it up and spending your funds.
To make things even more interesting, some wallets use a BIP39 passphrase (sometimes called the "25th word"). This is an optional, extra word you add to your seed phrase that creates a whole new, separate wallet. Forgetting your password, seed phrase, or this passphrase can mean your crypto is gone for good.
Is It Safe to Use an Online Wallet Recovery Service?
That all comes down to how they operate. A legitimate, trustworthy service will always be non-custodial. This is the most important thing to look for. It's a fancy way of saying they should never ask for your seed phrase or your unencrypted private keys. Ever.
A secure recovery process is built so that you, and only you, ever have control of your crypto. The service provides the specialized tools and heavy-duty computing power to help you find your password, but they should never be in a position to touch your funds. Always stick with services that are completely open about their methods and put your privacy first.
If you're staring at a locked wallet because of a forgotten password or a corrupted file, Wallet Recovery AI offers a secure, non-custodial way to get back in. Our AI-powered process is designed to give you the best possible shot at success, all while keeping you firmly in control of your assets. Find out more and get started on your recovery at https://walletrecovery.ai.


Leave a Reply